Covid-19 Archive
Our Covid-19 archive chronologically documents all our articles from the period 13 March 2020 to 3 August 2022 concerning the global pandemic.
The events over the affected years following the announcement of the first national lockdown on the 23 March 2020 presented numerous challenges for all businesses, employees and employers alike.
We documented the schemes, restrictions and legislations in order to support our clients during the pandemic, with articles covering topics such as (but not limited to) furlough, grant payments, deferral of VAT payments, job retention schemes, returning to the workplace, support for businesses, preparation for post Covid-19.
Navigating the schemes being introduced whilst supporting our clients was paramount during this period of uncertainty. Our archives contain the expert advice and updates that we communicated, as well as retaining useful information and resources that you may wish to refer back to.
Business support
Support for businesses that missed out on Government funding
The Government’s support for small businesses has been unwavering and local councils, in the main, have administered the monetary assistance quickly. However, we know that no two companies are the same, nor are their needs during the pandemic.
You must act now. Application deadlines range from the middle to end of June 2020.
We have seen those receiving small business rate relief, rural rate relief, and those in the retail, hospitality and leisure industry, issued with a one-off grant of £10,000. The Government realises though that there are small businesses that have not yet been supported but have high fixed property costs which are seriously feeling the effects of the pandemic.
Local authorities in England have a sizeable discretionary fund worth £617m to support businesses that have not been eligible for the small business or leisure grants. They will aim these funds predominantly at helping:
- Small and micro-businesses (under 50 employees)
- Businesses with relatively high ongoing fixed property-related costs
- Businesses that can demonstrate that they have suffered a significant fall in income due to the COVID-19 crisis
- Businesses that occupy a property, or part of a property, with a rateable value or annual rent or annual mortgage payments below £51,000.
The largest grant available is £25,000, this then drops to £10,000 and the local authority have discretion for any amount under £10,000.
The fund has been set up in the main to support property costs, but the local authorities have the discretion to use their local knowledge to help those in need. The local authorities have a fixed amount of funds and will, therefore, be prioritising:
- Small businesses in shared offices or other flexible workspaces, e.g. units in industrial parks, science parks and incubators which do not have their own business rates assessment
- Regular market traders with fixed building costs, such as rent, who do not have their own business rates assessment
- Bed & breakfasts which pay council tax instead of business rates: and
- Charity properties in receipt of charitable business rates relief which would otherwise have been eligible for small business rates relief.
Due to having a limited amount per local authority, many have given application closing dates. These, in the main, are ranging from the middle to the end of June.
Businesses should submit applications through their relevant local authority website. You can find details on your local authority here including applications and closing dates.
Your local council will ask you to complete a declaration confirming that you will not exceed the relevant state aid threshold, and you were not an ‘undertaking in difficulty’ on 31 December 2019 (only applies to the COVID-19 Temporary Framework).
Eligibility
You will not be eligible for the local authorities discretionary fund if your business is already eligible for:
- The Small Business Grant Fund
- The Retail, Hospitality and Leisure Grant Fund
- The Fisheries Response Fund
- Domestic Seafood Supply Scheme
- The Zoos Support Fund
- The Dairy Hardship Fund
If your business is in administration or insolvent, it will also not be eligible for the scheme.
However, if you have applied for the Coronavirus Job Retention Scheme, you are still eligible. You must have been trading from the business you are claiming for, from at least the 11 March 2020.
If you already get state aid then the discretionary grants fund counts towards this threshold:
- £10,000 payments or less count towards the total de minimis state aid you’re allowed to get over three years (€200,000). If you have reached that threshold, you may still be eligible for funding under the COVID-19 Temporary Framework.
- £25,000 payments count as state aid under the COVID-19 Temporary Framework (€800,000).
This blog was written by Matthew Hector, a Manager at Price Bailey. For further information relating to this article, or any other COVID-19 related support you can contact Matt on the form below.
Navigating the post-COVID ‘perfect storm’
It may not surprise you that there is a general expectation amongst insolvency practitioners (and beyond) that a significant rise in corporate financial distress and, therefore, formal insolvencies are on the horizon.
Many commentators, though, have used the phrase ‘perfect storm’ to describe the potential severity of the situation we may all be facing. Current historically low failure rates may mask the growing number of factors that could converge to make 2021 the toughest trading year in living memory. Why might there be such choppy waters ahead?
The (more obvious) factors include:
The end of government support
The raft of measures, including CBILS & BBLS, the furlough scheme and VAT deferrals, clearly cannot go on forever and will need to be repaid. Sectors such as hospitality and leisure have suffered significantly and, without wishing to state the obvious, the damage will take a toll on many. Within the insolvency profession, there has been much talk about ‘kicking the can down the road’ each time support is extended. While the availability of support is to be commended, there is a growing sense of saving up problems for another day.
Catch-up
Official figures show that UK insolvencies in 2020 were at their lowest since 1989 and 40% down on 2019. Clearly, this isn’t because more businesses are thriving than in the previous 30 or so years. Rather, it suggests some of the measures introduced to help otherwise good and profitable business have also served to artificially prop up those businesses that were already doomed and would have failed. Measures such as the prohibition on winding up petitions, unless the reason for non-payment was non-COVID related (good luck proving that!), have held the number of business failures artificially low for the last 12 months. It cannot be the case that the injection of ‘COVID cash’ and creditor forbearance have turned these otherwise failing businesses into profitable entities. Aside from the unlucky casualties of the pandemic, a spike in insolvencies just to return us to where we would have otherwise been should be expected.
Other important factors:
The return of Crown Preference
For those old enough to have been in business before 2002, you might remember that HMRC used to be able to claim ‘preferential status’ (i.e. would be repaid before other unsecured creditors) in formal insolvencies.
From December 2020, HMRC became a (second-ranking, behind former employees) preferential creditor again regarding some taxes, most notably VAT, PAYE and National Insurance. This places the Crown back ahead of banks and funders with floating charges, making those lenders more vulnerable when a company enters an insolvency process.
The Enterprise Act introduced the concept of the ‘prescribed part’ – where some of the cash otherwise due to a floating charge holder was instead paid to unsecured creditors. The ‘quid pro quo’ for this change was that HMRC’s preferential status would stop, and they would be repaid the same proportion as other unsecured creditors, such as trade suppliers. The new Crown Preference provisions come with no such counterbalance to ensure the banks are no worse off in an insolvency situation.
The proposed reintroduction of HMRC preferential status attracted much criticism when announced (even in the good old pre-pandemic days). I was one of many that suggested that the likely damage to the UK’s rescue culture would far outweigh any potential benefits to the Treasury. With all the government assistance afforded to businesses in the last few months, it seems incredible that HMRC’s proposed bump up the pecking order was not postponed at least.
For example, preferential creditors cannot be bound by a Company Voluntary Arrangement (CVA) without their consent. As such, unless the company hoping to enter a CVA to trade its way out of difficulties is confident of repaying crown debts in full, HMRC now effectively hold a veto on the entire process. Moreover, even if HMRC can be repaid, it is very common in the current climate for businesses to have large tax arrears from taking advantage of the option to defer VAT and PAYE payments. The need to find these amounts in full, ahead of all unsecured creditors, is likely to make many proposals simply unworkable, meaning that ‘terminal’ rather than ‘rescue’ proceedings may be the only possible option.
The banks
Barclays recently reported a 30% fall in pre-tax profits for 2020 and has set aside £4.8 billion for loan defaults due to the economic fallout of the pandemic.
A change in accountancy regulations brought about by IFRS 9 (stay with me!) means that the way the banks recognise these losses will change. Previously they would have only been recognised once the loss incurred. The movement to an ‘expected’ loss model, meaning that these lenders must fully recognise anticipated credit losses in the financial year relating to any loan default. Simply put, the banks’ balance sheets will take a bigger hit all the sooner.
The implication of this and the reintroduction of HMRC’s preferential status is that would-be lenders are likely to become less willing to advance new cash. Unless a company has significant assets, access to finance – especially in a rescue context – is expected to become more difficult.
Lenders might also seek tighter covenants around HMRC payments and greater control of book debts to maintain a fixed charge claim over such debts. In some instances, this might limit directors’ ability to manage immediate cash flow difficulties, removing an often important lever to defer HMRC payments in the short-term.
Pre-pack bashing
They don’t have the best of reputations, driven in no small part by media misreporting, but pre-packaged administration sales (where a buyer is found before a company entering administration and the business and assets are sold with little or no notice to creditors) are an important part of the UK rescue culture.
Numerous government attempts to ‘clean up’ the use of this procedure and improve ‘stakeholder confidence’ have been introduced, the latest of which seeks to make it mandatory for management looking to buy-back a business to employ an independent (but unlicensed) Evaluator. Whilst it can never be a bad thing to increase scrutiny and transparency of such a process, I have little doubt that the criticism of pre-packs has been somewhat overstated. Any IP entering into a pre-pack already has a staggering amount of hoops to jump through to agree and justify the outcome to creditors. The introduction of another barrier seems unlikely to provide any party with any real comfort but will further increase the costs of the process.
Crisis or opportunity?
I don’t wish to paint an unnecessarily pessimistic picture here. It is a common misconception that all insolvencies are bad (and far be it from me to suggest to anyone losing their business or their job to ‘cheer up & look on the bright side’). On an individual level, it is a tough and emotionally draining process for business owners to wind up a company’s affairs after many years and one I never take lightly.
On a more macro-economic level, however, insolvencies serve a vital function for the economy. At best, rescuing viable businesses and preserving jobs is often misunderstood and undervalued (I would say that, I suppose). Even at the lower end of the scale, terminal liquidation procedures, where a business often cannot be saved, serve to recycle assets into the economy and provide opportunities and new growth.
New legislation under the Corporate Insolvency and Governance Act 2020 or ‘CIGA’ (more on that another day perhaps!) has sought to improve the rescue landscape within the UK. My concern, however, is that many factors are potentially conspiring to make the use of tried and tested rescue procedures such as Administrations and CVAs less viable.
Focussing on the positive, the seemingly inevitable rise in insolvency rates affords those well-run, agile businesses with cash reserves and/or quick access to finance many new opportunities for acquisition and growth in the coming months and years. If you look hard enough and plan your journey carefully, perhaps there are some calmer waters to be found and some sunlight poking through the storm clouds ahead.
This article was written by Stuart Morton, Insolvency and Recovery Director at Price Bailey. If there is anything in this article that you would like to discuss or find out more about, please contact Stuart on the form below.
What is the new guidance for living with COVID-19?
On 21 February the Government published its plan for living with COVID-19. Below we have summarised the changes and their potential impact.
What are the changes and when do they come into effect?
21 February 2022
- Guidance for those in education and childcare settings to test twice a week was revoked.
24 February 2022
- Employees are no longer required to self-isolate if they test positive for Covid-19, or if they have been in close contact, regardless of vaccination status. However, the Government guidance is that those testing positive should stay at home and self-isolate for at least five full days, and until there have been 2 negative test results on consecutive days. This guidance will be in place until 1 April 2022.
- Workers, therefore, are no longer legally obliged to tell their employers when they are required to self-isolate.
- Contact tracing has stopped and those who have been in close contact are no longer advised to isolate or take daily tests. Instead, guidance will set out precautions advised for those who live in, or, have stayed overnight in the same household as a positive case to reduce risk to other people; other contacts will be advised to take extra care in following general guidance for the public on safer behaviours.
17 March 2022
- The Statutory Sick Pay (SSP) rebate scheme will close. Employers will no longer be able to claim back SSP for their employees’ COVID-19 related absences or self-isolation that occur after 17 March.
24 March 2022
- The special provisions for SSP for those absent from work because of Covid-19 will be removed, meaning someone will have to be unfit to work in order to be entitled to SSP, and the usual three-day waiting period will apply.
1 April 2022
- Guidance issued advising those testing positive for COVID-19 to stay at home will end, and those with COVID-19 symptoms will be encouraged to exercise personal responsibility (as those who may have flu are encouraged to be considerate to others).
- The ‘working safely’ guidance will be removed and general public health guidance will be issued which will set out the ongoing steps that people with COVID-19 should take to minimise contact with other people.
- Employers should continue to consider the needs of employees at greater risk of serious illness from COVID-19. The Government will consult with employers and businesses to ensure guidance continues to support them to manage the risk in the workplace.
- The Government will no longer provide free universal symptomatic testing for the general public in England. However, free symptomatic tests for the oldest age groups and the most vulnerable to COVID-19 will be provided. The Government is working with retailers to ensure that tests will be available to buy.
- The Government will remove health and safety requirements for every employer to explicitly consider COVID-19 in their risk assessments. The intention is to empower businesses to take responsibility for implementing mitigations that are appropriate for their circumstances.
- The Government will no longer recommend the use of voluntary COVID-19 status certification, although the NHS app will continue to allow people to indicate their vaccination status for international travel.
What are the practical implications?
An increase in those attending the workplace with COVID-19 represents a risk to businesses – as an outbreak amongst a team could jeopardise the ability to continue functioning effectively.
Employees refusing to attend the workplace because of concerns also represents a practical risk in terms of getting work done and management’s time spent dealing with it.
What are the legal implications?
Employers still owe a duty of care, and therefore it is still important to take measures to assess and reduce risks to your workers.
Taking an approach that is at odds with the guidance will make it difficult to discipline employees who wish to self-isolate following a positive lateral flow test result. It is therefore advisable to continue to keep positive cases out of the workplace until the guidance changes on 1 April.
Can employers require people to stay at home, even if they are physically fit?
You could implement workplace rules/policy regarding COVID-19 which would require someone who becomes aware they are positive to stay at home – either working from home or not working at all if they cannot work from home. It is unlikely that a requirement to work from home or stay at home isolating if positive could be argued as being unreasonable unless there is a significant detriment (see ‘what about pay’ below).
What about pay?
If someone is off work with COVID-19 symptoms as they are not fit for work, they are entitled to SSP (or company sick pay depending on your policy) from day one. However, from 24 March you will no longer have to pay SSP from day one, and the usual three day waiting period will apply.
If someone has tested positive but has no symptoms, they can be asked to work from home and should be paid as normal.
If someone has tested positive but has no symptoms, and you require them to stay at home but they cannot work from home, they will be entitled to SSP from day one until 24 March. However, please be aware that if you do have a policy of only paying SSP for employees self-isolating in accordance with government guidance, this does run the risk of potentially infected employees failing to inform you of their self-isolation requirements, so they can continue to attend work and receive pay. Employers should therefore think carefully about their position on pay during self-isolation in these circumstances.
If an employee is a close contact of someone who has tested positive, or, if you require them to stay at home and they cannot work, then subject to any contractual provision to the contrary, they will need to be paid in full.
From 24 March, if someone is physically fit to work, and is ready and willing to do so, but you require them to stay at home (because they are asymptomatic, or have been in contact with someone who has tested positive) and they cannot do their job from home, you will need to pay them in full.
What steps should I take?
- It is sensible to continue with any COVID-19 health and safety measures in place currently. These will help mitigate the impact of an increase of COVID-19 in the workplace.
- Consider purchasing testing kits, to reduce the problem of lack of testing.
- Decide what your policy will be if someone tests positive, in terms of working from home or requiring them not to attend.
- Set out your policy on pay for those with COVID-19 or those that are isolating, and communicate this to employees.
- Consider what your position will be for those who are reluctant to attend the workplace. It is still advisable to take steps to address concerns and take into account any personal circumstances, but given that the guidance to work from home has come to an end, it will normally be reasonable to expect healthy employees to return to the workplace if required to do so.
When more guidance is available, we will update you on its content and the potential impact on employment decisions.
Job Support Scheme calculator
You can use this Job Support Scheme calculator to help you quickly and easily work out your employees’ pay and the various contributions that need to be made under the Government’s new Job Support Scheme (JSS). Use it to find out how to scale back your employee working hours, if needed to retain staff.
Please note: The Job Support Scheme is being delayed due to the extension of the Coronavirus Job Retention Scheme or more commonly referred to as the furlough scheme.
Preparing for your first audit in a post-COVID world
The role of the auditor has been under increasing scrutiny over the past few years after some high-profile collapses. If anything, the impact of the COVID-19 pandemic has served to bring that into an even sharper focus.
At the same time, new auditing standards, ISA 540 on Accounting Estimates and ISA 570 on Going Concern, have been issued to provide further clarity on the responsibilities of auditors and the expectations of both auditors and company directors. These new standards focus further on the requirements of the auditor to sufficiently challenge management assertions and representations and demonstrate sufficient scepticism.
Given these changes, company directors may be left wondering how these changes will affect their company, particularly their first post-COVID audit. Our conversation with Corporate Partner, Darren Amott, may help to address any pressing questions they may have in this respect.
In this video, Darren talks about the changes occurring in the audit world and the potential impact of COVID-19 on company financial statements and the audit report. He also provides advice on how best to prepare for your upcoming audit and the additional questions you can expect from your auditor.
How do we value a business in the post-COVID era?
This time last year, we wrote an article on valuing a business in the COVID-era. A year on, and in circumstances that more closely resemble a normal that we all recognise, we revisit the topic to see what has changed and is changing for business valuations in today’s world.
An issue that came about this time last year and is still debated is, is the last two years at all relevant to valuations? Instead, is the focus on now, with more emphasis on budgets and forecasts from here forwards? It is our, and the opinion of many valuation experts, that the very definition of a valuation ought to be about the future cash flows of the business, and COVID-19 has highlighted how recent past results can be very irrelevant to future opportunities. Increasingly we’re talking about what is happening today, what is the budget for the next 12 months and what is the direction of travel?
Additionally, conversations are rapidly moving to post-COVID issues, such as the impact of the war on Ukraine, the value of the pound, and whether oil or commodity prices or interest rates are going to rise further. In many ways, business concerns are now moving beyond COVID.
That is not to say that consideration should not be paid still to the performance impacts of COVID; in many instances, the events of the last two years have created significant changes in how certain businesses operated. Therefore, while the performance of 2020 and 2021 may not be repeatable, it may very well have influences over what today has in store.
With that, we take to looking at areas of performance that are central to this debate.
Revenue expectations
This might be still something that is fairly difficult to forecast. However, in our role as valuation experts, we would ask our client to focus on comparisons of pipeline today with a pipeline that would have been expected in the 6 months from 01 March 2020, in spite of COVID. For instance, if a business would normally have the next 6 months of sales in its pipeline, what has it got today? And what does it look like?
The follow up to that is then whether the next 6 months sales are owed to catch up, a bubble from missed sales or the emergence new markets. If it is, can the underlying business meet current demand in a short space of time? Some businesses can because they have the capacity to catch up, whereas other businesses can only do a certain amount of revenue in a month, so the only thing they can do is change the price, not the volume. Some businesses are also severely resource constrained at the moment – whether it be microchips or steel – so this also needs to be considered.
Looking at the individual business and understanding the drivers of that business is vital, but we also need to understand the variables that the business can control compared to those that the market controls. The more variables the business can control, then the higher quality of valuation they are going to end up with.
Cash flows
Cash will remain a very important tool to have, as it allows a business to buy quickly, avoid needing to use credit and that does give you some price advantage on the buy-side. All of that said, there is still a lot of care needed to ensure there is some proper credit control going on.
- Government support repayments – CBILS or Bounce Back loans were hugely successful in supporting businesses. We are now over a year on from when they were first available, and repayments on the majority of facilities will have started. Many of these businesses, however, will not have used some or all of them, meaning that this cash is sitting in the bank ready to be repaid, or already paid off. Consequently, in these circumstances, adjustments for repayments to cash flow and performance are now largely irrelevant.
- Credit control – In the first lockdown, businesses focussed on cash and cash collection. Since then, as business has slowly returned to normality, some of those working capital gains from year one have been lost and old ways of debt collection are returning. Understanding the extent to which tighter cash collection can be maintained or not, again, highlights the need to not rely on the past and look to the future – has the business changed or can it change its credit terms? Has it employed or outsourced more credit control resource to support with debtor collection? An efficient cash cycle remains a source of premium attraction in valuations.
Working capital
The normalised working capital calculation in valuations will continue to require careful consideration. The impact of COVID and those periods where businesses were closed, grants were coming in to cover costs, tax deferrals and rent free periods created real skews to the actual working capital both then and now.
An approach we have taken with clients is to separate out the normal adjustments from the COVID ‘special’ adjustments. Taking VAT as an example, we continue to treat the latest quarter’s VAT as a working capital item, but the deferred VAT from 2020/21 that is being repaid will be treated as debt, rather than working capital. We would therefore extract deferred VAT from the working capital calculations and add in to the debt calculations in both the average and the actual comparison.
Justifying a premium
It is incredibly important to look at the underlying business and the story around future performance expectations and assumptions, rather than just looking at a set of black-and-white accounts and assume you can tell what the important factors of the business are.
Methodologies
We aren’t seeing alternative valuation approaches being used, but there are some more interesting metrics appearing. For example, we’ve seen EBITDAC (Earnings before interest, tax, depreciation, amortisation and COVID) being introduced – but there is still a need to properly assess whether any adjustment for COVID is a proper and normal adjustment, and ensure you’re able to reasonably justify it.
We are challenging far more on the adjustments being presented, but also putting ourselves under scrutiny on the adjustments that we propose to make.
- Multiples – If the transactions within a dataset that is being relied upon for a multiple occurred during the pandemic then it is vital to understand the true underlying earnings within the businesses involved in each transaction. If that’s not obvious from the data available, then it may require looking into the transactions on a case by case basis to identify those that are relevant. Often databases will provide the high level figure that may or may not have scrutinised to ensure all the transaction data input into it is relevant. Relying on these too heavily, or without additional research, can be misleading.
- Scenario and sensitivity analysis – In theory, we want to be able to put some scenarios and probability analysis through to get an idea of the likely valuation parameters, but if there isn’t a base forecast in place already, then it is difficult. Unfortunately, this is often the case in SME businesses. We are already spending more time with clients this year to encourage them to work on their base case forecasts first. Having such forecasts and sensitivities available is not just helpful for valuations, but ideal management information to plan with. Whilst none of us predicted a pandemic, as we sit today we can look at the impact of varying levels of increased interest rates, temporary excess energy and fuel costs and the inflationary impact on pricing, sales, materials costs and wages.
Predictions for 2022
Both valuation experts and their clients will need to be prepared to explain any COVID adjustments, provide suitable evidence in support, and set out what future pipeline is expected to look like. Businesses should prepare for future performance to be the subject of as much, if not more, scrutiny as any historical data.
With this, we’d expect a higher proportion of M&A deals to have earn outs, and for those earn outs to be higher proportion of overall consideration on the deal.
This article was written by Simon Blake, For any questions regarding this article, you can contact Simon on the form below.
Cash flow management – Why and how in today’s climate
Cash flow is often monitored far more closely in times of uncertainty or change.
Many will now be closer to their cash flow than ever before, but how is best to manage it? What tools are available to continue monitoring after the pandemic? And how do you recover funds you are entitled to but have not been paid?
We hosted a webinar with our panel of in-house experts Matt Howard and Lee Sharman, who discussed:
- The importance of understanding where you are now to help better forecast for the future
- Tools for effective cash flow management, and how to identify and resolve common issues
- How dispute resolution and debt recovery can support you being paid as a priority over others; whilst mitigating risk, cost and being time efficient.
Thank you to everyone that attended. Here are the slides and recording from the webinar in case you would like to review them.
Webinar slides
If you would prefer you can download a copy of the slides below.
Download webinar slides
Webinar recordings
If you would like to watch the webinar again you can access the full recording below:
We aimed for the session to be interactive and hope we answered a number of questions. Some we have followed up with directly after the event. If you have any other questions following the webinar series and would like to discuss these with one of our experts, please complete the form below.
The commercial property market during COVID-19: a reflection
Economic pressures since the start of the Coronavirus pandemic has resulted in increased difficulties and complications for both landlords and tenants.
Many commercial property owners will have been impacted by tenants being less able to keep up payments – particularly those in the retail and hospitality sectors – with many left considering the provision of concessions relating to rent (including deferrals, rent holidays and rent reductions).
Covenant waivers and improved terms regarding loan repayments were introduced in an attempt to provide support to commercial property landlords, however these require careful planning with banks and tenants, and lenders’ outlook towards these developments have recently begun to change. The reasons above, amongst others, have resulted in the fluctuation of commercial property valuations throughout the pandemic.
This article goes some way into exploring the impact of the pandemic on the commercial property market and offers an auditor’s perspective on managing developments.
The immediate impact of the Coronavirus pandemic on the commercial property sector
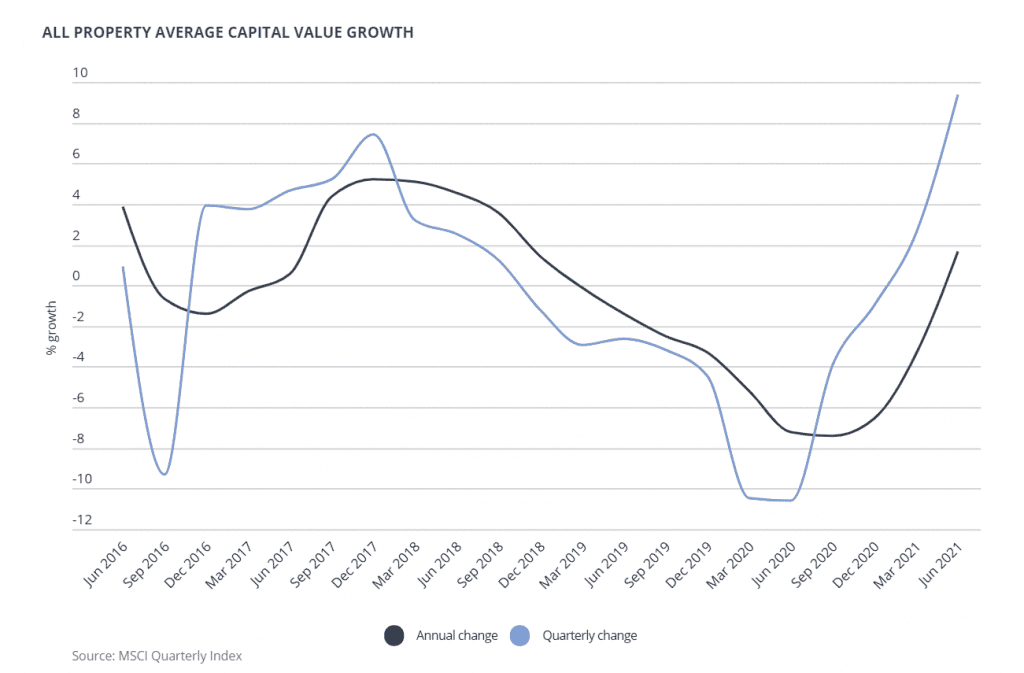
When lockdown restrictions were announced by the government, the majority of commercial property owners were immediately affected, with restrictions particularly impacting the hospitality and retail sectors. Although, with the government’s ‘stay at home’ order, many office spaces and manufacturing businesses were also left abandoned. In the year to June 2021, Morgan Stanley Capital International (MSCI) data stated that rental value growth for office and retail remained between -0.2% and -6.2%, compared to 2018 where rental value growth for retail was between +0.5% and -3%, and rental value growth for offices remained above +1.5% and below +2%.
The low levels of retail rental growth experienced prior to the pandemic is in part due to changing consumer habits and low consumer confidence levels. However, a decline in growth for office rentals represents the immediate impact of the pandemic on office landlords and tenants alike.
The circumstances of COVID-19, alongside the low growth in commercial rental values left commercial property landlords in a difficult position. They faced uncertainty around the future viability of their tenants, further uncertainty around their ability to find new tenants should their current tenants close/ fail, and thirdly, the overall value of their main assets i.e. the properties, was stagnating and potentially threatening to shrink given the 2021 rates referenced above. Consequently, numerous landlords had to be creative about how they dealt with this sudden shift in their market, through both reviewing their position, and working in collaboration with their tenants and banks to mitigate any negative impacts.
What was the effect of the restrictions?
Property valuations became increasingly challenging
The uncertainty in the market created by the COVID-19 pandemic and the resultant shrink in rental values made it increasingly difficult to value property both during the lockdowns and subsequently as restrictions have eased.
For surveyors, this meant including large caveats in many valuations, particularly with regard to the economic impact on the market and the future viability of the properties. All major valuers subsequently introduced a material uncertainty qualification for valuations dated 31 March 2020 and onward.
Auditor’s perspective
As valuing a property is more difficult than ever, this means that auditing these valuations is equally difficult. Auditors have therefore either had to rely on other means to assist in substantiating values, such as reviewing the strength of tenants, the yields, and other factors in more detail. In many cases, particularly at the outset of the pandemic, auditors were unable to adequately quantify the valuations, resulting in a ‘Limitation of Scope’ or an ‘Emphasis of Matter’ paragraph being included in the audit report in respect of the property values.
As valuations stabilise in the future, auditors face three major issues
1. Being sure surveyor’s valuations of commercial properties are accurate
2. The ongoing concern in light of liquidity restrictions, covenant breaches and tighter lending
3. The recoverability of rent arrears as a result of new restrictions that will be imposed
Defaulting tenants
As a result of the Coronavirus pandemic many businesses were forced to close their premises, which for the majority of these businesses meant temporary closure of operations too – particularly if their business model could not easily be adapted to be online or virtual. This resulted in a number of businesses defaulting on their rent payments or making use of rent deferrals and repayment holidays, due to cash shortages.
Defaulting tenants, unfortunately, also have a negative impact on the value of commercial property. When a surveyor is valuing the property, amongst other factors, they analyse the quality of the tenant and the length of the lease, as this provides an indication for future uses of the property. If you have a strong and established client in the premises with a longer lease, this will likely increase the valuation of a property compared to less established tenants on shorter leases.
Auditor’s perspective
Currently, there are a significant number of rent arrears in the market with landlords often unable to enforce debt collection. From an audit perspective, they have to audit recoverability of those debts – this will be a difficult judgement on the part of directors – and auditors will need to ensure they are as comfortable as possible that these judgements are sound and based on robust assumptions.
At the start of the pandemic, the government recognised the initial risks of cash shortages and defaulting payments, and responded efficiently by introducing varying legislation and schemes to support tenants, including; rate rebate, Furlough, Coronavirus Business Interruption Loan Scheme (CBILS) and the Bounce Back Loan Scheme (BBLS). In addition, the Corporate Insolvency and Governance Act (CIGA) which covered areas such as a moratorium protecting tenants facing problems with rent repayments as a result of COVID-19, included other specific legislation regarding the rights of tenants and landlords during this period.
Corporate Insolvency and Governance Act (CIGA)
On a larger scale, the CIGA hindered the ability of landlords to recover any unpaid rent from tenants. So whilst tenants received vital support from the government, some landlords were left feeling ignored and under financial pressure if they faced cash flow issues themselves.
Whilst the Government saw CIGA as vital for preventing wholesale eviction of tenants, it has created apparent problems for landlords – with commercial landlords leveraged to varying degrees and still having to make their loan repayments; many relied on their banks to be understanding and agree repayment holidays. The Government have recently extended the restriction on rent related forfeiture of business tenancies until 25 March 2022, which means commercial landlords will continue to have limited powers until then.
The Government have also announced that a new Act of Parliament may be enacted to address the rent arrears that have built up since the start of the coronavirus pandemic. The details of this Act of Parliament remain relatively unclear for now, however it is likely that landlords will have to take a rent cut where tenants were forced to close during the pandemic. It appears that this is an attempt by the Government to further reduce the chances of a surge in insolvencies as soon as the CIGA restrictions are removed. This fear of insolvencies once the CIGA restrictions are removed, is particularly prevalent in the retail and hospitality industries.
Impacts for landlords
The limitations of CIGA regarding actions landlords could take against tenants for non-repayment of rent left many feeling disappointed, with many commercial property landlords also highly leveraged with tight banking covenants that pre-dated the Coronavirus pandemic. In the event that tenants defaulted on rent to the extent that loan repayments on the part of the property owners could not be met, there was (and still remains, given the extension of CIGA) the risk of covenant breaches. In many cases, a breach of this nature often triggers a clause that means the loans technically become repayable immediately. Whether or not this is enforced by the bank – the effect is that the loans often move from ‘creditors due in more than one year’ to ‘creditors due within one year’. On paper this significantly weakens the landlord’s balance sheet, potentially putting the business at risk. If however, the landlords is proactive and is able to obtain a waiver from their bank in advance of the year end, then the loan can continue to be reflected as due in more than one year.
For commercial property owners that were at risk of the knock-on effects of their tenants not being able to pay their rent, they were advised to sustain open communication with their banks in relation to the landlords defaulting on any loan repayments. Banks, under pressure from the Government and realising the extent of the situation, were initially sympathetic to covenant breaches and provided waivers and improved loan arrangements to commercial property businesses. However, banks are now generally becoming more risk averse to the property sector and as well as having a lower inclination for lending in the sector, are also beginning to restrict covenant ratios i.e. decreasing loan to value ratios.
Auditor’s perspective
Many businesses had tight banking covenants prior to the Coronavirus pandemic, and the pandemic meant that they were in breach immediately. This technically means that loans were due within one year of the breach. For auditors, they needed to assess what steps businesses and bankers took when, or ideally prior, to these breaches occurring, and whether any waivers were received, before assessing the impact in going concern.
What should commercial property owners be doing/thinking about with regards to their properties now?
Alongside an increase in covenant waivers and improved terms for loan repayments for commercial landlords, there has been a surge in progressive lateral thinking regarding alternative uses for property, including the conversion of premises to residential property and the conversion to serviced offices – which provides certain flexibilities to tenants. Whilst many commercial property holders have a diversifying portfolio anyway, some may take this as an opportunity to develop their existing holdings into residential property, given that this market is expanding. The ONS have reported that 41% of people are still working from home exclusively or part-time (time of writing: Sept 2021), which raises the question if offices will ever reach the levels of demand they were in before lockdown. However, because serviced offices offer short-term leases, they are great for tenants that want to be flexible and expand/contract as needed in line with their business plan. However, the exact outlook and what it will mean for valuations in the market remains unclear at this time.
Alternatively, there has been an increase in demand for different leases – including turnover based leases. This is where a part of the tenants rent is based on the level of turnover they achieve and are a great mechanism for engaging both the landlords and the tenants in a symbiotic relationship – when the tenant succeeds so does the landlord, and when the turnover the tenants generate is lower, this often incentivises the landlord to support the tenants. These types of leases have become popular recently in the UK in the retail and hospitality industries – and we suspect, will continue to gain traction – as a result of the pandemic, and tenants’ progressively growing bargaining power.
What is likely to happen next?
The economic downturn over the past 18 months has certainly affected some sectors more than others, including the hospitality and retail industries. The future for some commercial property tenants will be challenging as they will still need to repay their rent deferrals and bank loans, furlough will be withdrawn and full rates will need to be paid again. However, legislation such as the Act of Parliament will provide some protection to tenants that were forced to close during the pandemic. Commercial property landlords may also face a challenging time ahead; lower valuations and a change in outlook from the banks is likely to put more pressure on covenants and make it harder for landlords to obtain finance.
It is likely that both tenants and landlords will face a continuation of difficulty ahead with regards to ongoing uncertainty in the property industry, legislation developments and restriction of covenant ratios, amongst other factors. It is important that as a commercial property owner, you are proactive in communicating with your stakeholders. If you have defaulting tenants or are concerned about their continued ability to meet rental payments, it is advised that you speak to your bank and advisors as soon as possible. This should be in advance of a potential breach with the view to obtaining a waiver before the year end, to avoid unnecessary negative impacts on the company balance sheet.
If you are a tenant or a commercial property landlord, and require any further support regarding anything discussed above, then please contact Darren Amott using the form below.
Delaying import duty payments due to COVID-19
For businesses globally, the COVID-19 pandemic is creating an unprecedented amount of uncertainty. The Governments relief measures and certain HMRC payment deferrals are working to offset some of the cash-flow strains felt by businesses.
This now also extends to those businesses in the UK that trade internationally. Below we’ve set out the latest guidance from HMRC on the details of duty/import VAT payment deferrals. The latest announcement from HMRC for existing duty deferment account holders and non-account holders is set out below.
Duty deferment account holders
A duty deferment account lets you make one payment a month through Direct Debit instead of paying for individual consignments.
Duty deferment account holders who are experiencing severe financial difficulty as a result of COVID-19 and who are unable to make payment of deferred customs duties and import VAT can contact HMRC for approval to enter into an extended period to make full or partial payment, without having their guarantee called upon or their deferment account suspended. Account holders will be asked to provide an explanation of how Covid-19 has impacted their business finances and cash flow.
If you had deferred customs duties and import VAT due on 15 April 2020 and did not have sufficient funds to be able to make payment, Price Bailey advise that you contact HMRC immediately. Details of who to contact are listed on the HMRC website here.
“Duty Deferment account holders will be able to use their accounts during the extended payment period agreed unless they default on a subsequent payment in that period, in which case HMRC may consider suspending their account. The outstanding payment will not affect their duty deferment limit so they will not need to increase their guarantee to cover the outstanding payment. Where HMRC agree to an extended payment period, interest will not be charged on the outstanding payments provided they are paid in full by the agreed date.”
Duty/import VAT payments not covered by a duty deferment account
“Registered Importers who pay cash or an equivalent and are facing severe financial difficulties as a direct result of COVID-19 can contact HMRC to request an extension to the payment deadline at the time the payment is due. They will be asked to provide an explanation of how COVID-19 has impacted on their business finances. HMRC will consider this request and decide whether or not to agree an additional time to pay. The decision will be taken on a case-by-case basis and could be refused.
If the request is approved the conditions, including the length of time offered, will depend upon the importer’s individual circumstances and may require the holding of a guarantee for the period of the time extension. We cannot offer this facility to non-registered importers.”
Further information on customs duty deferrals can be found here.
If you are worried about duty/import VAT payments due for your business and are unsure on what you need to do, please contact us using the form below.
Legal sector round table: What lessons were learnt from the change in our ways of working?
Price Bailey hosted a round table in collaboration with Modern Law. By drawing on 12 voices from 12 legal firms across the country, we hoped to find out more about the important questions that have come out of the past 18 months. What lessons were learnt from the change in our ways of working, i.e. flexible working, virtual meetings, remote management?
Have these things led to an increase in bottom-line figures? What impact has this had on maintaining a firms’ culture and attracting new talent into the firm? How can firms look to maximise the opportunities out there, and will they look to add additional service lines in order to mitigate revenue stream risks?
Chair: What’s been the key lessons that you’ve learnt in the last 18 months, and what positives have come out of having to go into lockdown for your law firm? Has productivity increased?
Kicking off the discussion was Roger Bull, Burges Salmon LLP. “From the client perspective, our firm received an overwhelmingly positive response, and it also helped develop relationships because we were all fighting the same fire. I think there was some initial concern that the client relationships would suffer and, in turn, business development, but in fact, we found a lot more of our clients were willing to use technology to have a 20-minute meeting or catch up.” Roger goes on to speak about how it had also driven collaboration within their team. “People have pulled together with an absolute common goal. We’ve taken some real positives around transparency and communication – being a lot more open with what’s happening to the business, what the leadership thinking is and why we’re doing what we’re doing at this current time.”
Jessica Szczelkun, O’Neill Patient Solicitors, agreed with this view before adding her own insight to this question posed by the Chair. “We’ve found that a real positive has been how it’s built greater trust in our firm. We didn’t see productivity suffer; we saw it shift. Though our workforce was working slightly different hours and people would be logging in after the children had gone to bed, we supported that and were able to offer a more flexible style of working. I feel it has really helped strengthen the relationship across the board and has pulled us much closer as an organisation. There’s more accountability, and there’s more communication because we knew we had to make the effort to get in touch with people, rather than just being busy or doing all-day jobs.”
“Yeah, I completely agree with that,” says Nadia Biles Davies, Sharpe Pritchard LLP. “For us, there was a concern around a dilution of culture because everyone’s working further apart. However, actually, we’ve been working more closely than ever because you can have an all firm meeting, but you don’t have to get everyone in the room – everyone can join in. Nadia outlines some of the initiatives they have set up in order to keep the team connected and strengthen the culture of the firm. “We recently did a ‘Desert Island Discs’ where everyone had to share their island discs with a bit of a story behind it. It was actually the brainchild of our wonderful trainees, and by getting everyone from across the firm involved, within a few short months, we really got to know each other in a way that I think we wouldn’t have done before lockdown. In many ways, that culture of us all being in it together – like Roger mentioned earlier – meant that our culture continued to be enhanced as opposed to diluted.”
The hardest thing is to work out what makes an attractive client and then working out how to develop a relationship with them and how you can add value to that relationship.
Chair: That’s great to hear that you feel there have been huge positives for your firm. So, with that in mind, what’s your message about returning to the office for you as a firm?
“For us, it’s about trying to take your team along on your journey and providing that flexibility,” says Richard Baker, Stephens Scown LLP. “We’ve gone for, in principle, two days a week in the office but are leaving it very flexible. We wanted to allow our team leaders to make a lot of those decisions and have given them the training around that in order to try and balance what we call the ‘scowner’ experience (people who work here) with the client experience.” Richard believes it’s really important to provide people with flexibility because there are very genuine concerns coming out in the sector around well-being. “We’ve tried to pick up on them, but we haven’t necessarily seen the full extent of it yet. It’s not just about work, is it, it’s about what people have been through in their personal lives, whether that’s their parents, friends or other relatives who might have suffered – it’s been a very hard time for people.”
“With us, I don’t want to be controversial, but our experience has been a mixed bag”, claims Abu Kibla, Stuart Miller Solicitors.
“I found that many of our staff didn’t know how to manage themselves working at home. They actively called me and said, look, can I come back to the office? Surprisingly it was mainly the younger members of staff that did this.” For Kibla – whose firm litigates criminal cases – having your own caseload can be very isolating and what he’s seen is that most of his team are happy to be back in the office. “I see the connections that people have made since coming back, and though I share the sentiments of others around this table, in terms of the massive improvements in cost savings and being more efficient, I think on a human level when you take into account the type of work we do – it has been very difficult.”
Jeff Lewis, Brabners, picks up on the point that Kibla makes about junior members of staff. “That’s the one thing that we probably do need to keep a real eye on going forward – supervision, mentoring and training our junior people. As I always say to junior people or those that are newly qualified – you can read as many books as you like and go to as many training courses as you like, but actually sitting in the office and watching the people who have been doing the job for a long time is priceless.” Lewis explains that you need to make sure that there is still the ability for people to learn from those who have been doing it for a long time and has learnt over the past 18 months that this is not always the same when working from home. “We also need to make sure that our senior people have got people on hand who they can delegate the work to. Otherwise, it’s very easy for senior people to cling onto the work and say, well, I can do it faster myself, but that’s not doing the firm or the junior people any benefit in the long term.”
With everyone talking about the generational differences in wants and needs, Chris Godsave, Price Bailey, suggested people need to feel connected to other people and to place.

“Place plays a big part in creating that ethos and culture. If people are going to be working remotely, you might suggest that maybe the older generation – with their nice family homes and gardens – are happier to work from home than the younger generations who are in much smaller spaces. Consequently, there’s then a danger that your office is unevenly split between juniors and those with more experience.”
Chair: That’s an interesting point, Chris… how important do you think office space is in keeping your culture?
“I think it’s really important for the younger generation”, claims Ayesha Nayyar, Nayyars Solicitors. “A lot of the reasons they get these jobs in the city is to be a part of the whole graduate training vibe and comradeship. You want to enjoy those friendships where you go out for lunch/ dinner or drinks after work, and you want that network culture. I think we have to have an office so that even those members of staff who don’t come in regularly have still got somewhere to go.” In fact, Ayesha introduced an outside garden area at their office, which is something that she says would never have happened two years ago. “When the weather is lovely, it’s absolutely fabulous. Even on the colder days, they want to be outside because some of the staff have made it beautiful. Recently we’ve enjoyed a Euros party out there and have many more social gatherings planned now things are opening up – it’s great for the team spirit.”
After a short break, the Chair decided to move the conversation on to pastures new…
Taking the opportunity to pose a question was Chand Chudasama, Price Bailey, who asked if anyone had found the need to diversify how work is won? “I think for many lawyers, work is won through referral and cross-selling other services to the existing client base. This might be harder if we stay in a remote environment, but not necessarily. Have people found that digital marketing and other ways of attracting new clients has been high on the agenda?”
I definitely feel from a recruitment perspective it’s been massive. Most people we speak to that work in and around the legal sector are finding tremendous problems with recruitment.
“Definitely so. We’re quite systematic about it, and we do a lot of big data analytics to work out who we want to work with in order to segment the market”, states Stephen Crow, Clarion Solicitors. “The traditional approach for professionals is that you meet somebody for dinner or at some sort of event, you exchange business cards, and you might then convert them into being a client. However, the risk is that you then realise they’re not the client you wanted, or they might not want to pay for your service at all. The hardest thing is to work out what makes an attractive client and then working out how to develop a relationship with them and how you can add value to that relationship. That’s what we spend a lot of our time doing.’
Ian Jones, Backhouse Jones, followed this by explaining what they had done to diversify how their work was won. “We did two things, and we diversified into two areas: the training side we took online, and we set ourselves a modest revenue aspiration, shall we say. Thankfully, we completely smashed through that five-fold and we’re now charging for the training that we provide to the transport industry.” Ian goes onto explain how the other way that they expanded was equally interesting. “The one thing that I’ve always wanted to do for 20 years was take our brand and diversify it into an insurance brokerage. We had all this time last year where we could rethink our business model, and so we started BACKsure. Though it’s a different regulatory framework (which we had to get our heads around), it’s now up and running. So certainly, from a diversification point of view. we’ve done two things – BACKsure and BACKacademy.”
Coming in from a banking angle was Graham Martin, Barclays Bank. “Another model that I’ve seen being adopted is the consultancy model. A firm that I work with is very much a consumer, high-volume model, but about two years ago, they started to also introduce the consultancy model. What I’m now seeing is an escalation in this due to the flexibility of working from home and geographical restrictions being lifted. I’m not saying it’s right for every firm, but it’s certainly worked for that firm and has diversified their income stream so that when the conveyancing market does subside – they’ve got that model there as half their income. I definitely see that model having a place for firms going forward.”
Chair: Are you finding that the changes you’ve made to your firm are, in turn, changing the geography of your client base? Are you now picking up clients where geography isn’t important to them anymore? And same with staff as well?
Though most of the attendees around the table nodded in agreement to this question posed by the Chair, it was Joanna Kingston-Davies, Jackson Lees Group, who began the discussion. “I definitely feel from a recruitment perspective it’s been massive. Most people we speak to that work in and around the legal sector are finding tremendous problems with recruitment.” Joanna explains that they are now seeing city firms able to pay city rates to people who are not necessarily working in the city but instead are able to work in the countryside or less urban areas remotely. People are attracted by London or Manchester salaries without the need to commute anymore, so it’s huge. “I think client wise we’re seeing that a little bit less, although, obviously the fact that people can communicate with you via Zoom exclusively means that the opportunities are there – whether anybody has, I’m not sure just yet – but the opportunity I think is there for the taking.”
“One of our pushes has been on social media”, states Verity Slater, Stephens Scown LLP. “We’ve invested heavily in digital marketing over the years and punch well above our weight. In January of this year, DSMN8 ranked us the UK and Ireland’s 7th most active law and legal professionals on social media. That’s definitely brought in quite a lot of national clients for us that otherwise, you might not have attracted to the Southwest.” Funnily enough, Verity tells the group that they’re not having too much of a problem with recruitment because there’s an awful lot of people that want to get out of the cities and come and live with their families in the southwest (where they’re based).”For those that do want to leave the traditional city firm but also want a firm that has great work and a strong culture – we’re a strong choice. However, we are losing the odd person up the other way who are being attracted by corporate jobs. They’ve been enticed into going in-house for big nationals because they’re getting larger salaries and they’ve only got to go up to those places once or twice a week, whereas previously they wouldn’t have even considered that they could get a job with one of those firms if they lived down in the Southwest.”
Bringing the roundtable to a close, and from an interesting angle of a law firm working in the international arena, was Sunil Sheth, Fladgate LLI? “Personally, I think we’re seeing a talent war out there. Recruitment is a challenging process anyway, but over the past 18 months, it’s become more challenging because people have left the profession, and the development of associates has stalled because of not having the experience that they would have had working in the office. This has resulted in the salaries moving on an upward trajectory, and that’s been quite hard for us.” Despite the challenges, Sunil is quick to point out that there are plenty of opportunities too. “We found that people started thinking more about things like estate planning, wills, trusts and power of attorney because they were worried about what was going on.” He goes on to explain that about 30% of their revenue is also generated from foreign clients. “We’ve seen a lot of clients based abroad who think that Britain is a great place to be because our vaccine program is so far advanced, and we’re a safe haven for their funds. Consequently, we’ve recently set up a family office catering for high-net-worth individuals who have assets that need looking after from here – so there are obviously opportunities out there to diversify. But again, it’s a question of being fleet of foot and getting in there as early as possible.”
Conclusion
Earlier this year, Price Bailey hosted a roundtable with the aim of gaining a better understanding of how law firms were coping with the third national lockdown and the impact this was having on their law firms. Fast forward a few months, and after careful navigation of the government roadmap, Modern Law sat down with them again to discover what lessons have now been learnt, what positives there have been and how the attendees’ law firms had changed both from the inside and the out.
The discussion was hugely positive, and from the write-up, our hope has been to show you a slight glimpse into their experiences over the past 18 months. Not only did we hear that people had ironically come closer together during a time when we were told to stay apart, but the culture within the firms had grown too.
What‘s more, we heard how many of our attendees had adapted their businesses in order to win more work — whilst others told us of their excitement and need to be back in the office environment.
Yes, there were common concerns about the recruitment of talent after such a challenging year, but there was also huge optimism due to the perquisites of technology that have made geographical restrictions a thing of the past.
The pandemic isn’t going away any time soon, and we may never return to the normality we all knew before in the legal sector… but what this roundtable has shown is — is this necessarily a bad thing?
The impact of COVID-19 on corporate residence
With the global lockdown to quell the COVID-19 pandemic set to continue, what does this mean for corporate residence?
Under UK law, a company incorporated overseas will be subject to UK taxation if it centrally managed and controlled from the UK. Many other territories have a similar “central management and control” provision in their domestic legislation. With so many displaced people at the current time, this throws up two potential issues:
- Decision-makers stranded overseas risk creating a dual residency for any UK entities they manage
- For structures which rely on certain group entities being outside of the UK tax net, e.g. Guernsey or Jersey companies, the inability to travel to these locations to hold board meetings jeopardises the offshore status of these companies. It could result in significant profits being subject to UK taxation.
Certain tax authorities (the UK, Ireland, Australia) have already stated their position, saying they will be lenient and acknowledging that these are exceptional times. The Organisation for Economic Co-operation and Development (OECD), in its recently released guidance also highlights that it would be difficult for a state to assert taxing rights purely as a result of the short term impact of COVID-19 on the location of key individuals. For territories whose double tax treaty is based on the model OECD treaty, guidance around the “tie-breaker” clause discusses where senior executives “usually” or “ordinarily” carry out their duties, which provides businesses with comfort that a short term change in such arrangements is unlikely to have consequences.
However, as the crisis continues, we may see revenue-hungry territories start to challenge residency more aggressively. While the tax treaty network does provide a mechanism for attributing taxing rights and also dispute resolution, this is not a quick process. Equally, the outcome may be that while there is not ultimately double taxation, profits may be taxable in a higher tax jurisdiction. It is also worth noting that not all taxes are covered by tax treaties, and this is where local guidance is required.
For the time being, to provide the best possible support for a company’s residence, businesses must ensure robust record-keeping – where decisions have been made and why, citing, for example, local government travel restrictions.
In the longer term, COVID-19 related travel restrictions are likely to persist for some time, and it is expected that there will future episodes of lockdown around the globe as countries continue to grapple with the pandemic. With this in mind, businesses should give thought to the parts of their group structure that are particularly sensitive as far as residency is concerned. For example, those entities in territories where there are no permanent employees or UK companies whose directors are not physically in the UK all of the time because their family and permanent home is overseas. This will enable businesses to consider what mitigating strategies might be put in place, for example, the appointment of a local director, to provide more certainty in a landscape where free international movement of people can no longer be taken for granted.
This post was written by Sarah Howarth, a tax specialist at Price Bailey. If you require any questions relating to corporate residence, please contact Sarah on the form below.
Growth beyond the lockdown: webinar slides and recordings
How we do business is changing beyond recognition, through innovation and necessity. We believe that those businesses that are quick to adapt can not only survive but thrive in a post-lockdown world.
Over the course of three weeks, we hosted a series of webinars along with a panel of experts, to look at the opportunities that we expect to arise from the crisis. As well as discussing what growth strategies successful businesses should focus their efforts on in both the medium and long-term.
Thank you to everyone that attended. Here are the slides and recordings from the webinar series in case you would like to review them.
Webinar slides
If you would prefer you can download a copy of the slides below.
Webinar recordings
If you would like watch any part of the webinars again you can access the full recordings for all three webinars below:
Webinar 1: Future opportunities for organic growth – the five key growth decisions
Webinar 2: Growing by acquisition and selling your business.
Webinar 3: Evolving business models – what choices will growing businesses have to make now?
We had a really interactive session and answered a lot of questions. Some we have followed up with directly with those that asked, after the series. We understand, however, you may have any other questions following the webinar series and if you would like to discuss these with one of our experts, please complete the form below.
Temporary Insolvency law amendments – Wrongful Trading
18 June 2020
On 28 March 2020, Business Secretary Alok Sharma announced measures designed to support businesses experiencing distress as a result of COVID-19. These included the temporary suspension of wrongful trading provisions for an initial period of three months (from 1 March 2020 to 31 May 2020) which have later been extended until 30 June.
What is wrongful trading?
A business can be classed as insolvent if it can’t pay debts as and when they fall due (cash flow basis) or if the value of its liabilities exceeds its assets (balance sheet basis).
When a company is insolvent, the directors must continue to discharge their duties but have an overriding duty to act in the best interest of the company’s creditors.
If a business continues to trade while insolvent, it risks making the position worse for creditors, who may continue to supply goods/services on credit with no prospect of repayment.
Wrongful trading is a provision of UK insolvency law that is designed to deter directors from continuing to trade an insolvent business by making them personally liable for certain debts of the business.
If a director knows, or ought to have concluded that there was no reasonable prospect the company would avoid going into insolvent liquidation, the Court may order them to make a personal contribution to the company’s assets.
What does that have to do with COVID-19?
COVID-19 has had two notable impacts for directors in respect of wrongful trading:
- The immediate shock of the COVID-19 pandemic may have already created an immediate cash flow insolvency in some businesses.
- There is no certainty as to when the effects of COVID-19 will end, nor what their eventual impacts may be (prolonged staff illness, supply chain disruption, loss of customers, bad debts, etc.), thus bringing medium-term viability into question.
As a result, directors may already be questioning whether they ought to reasonably conclude that the business is, or is likely to become, insolvent.
Newly introduced Government support schemes themselves may also increase a Company’s liabilities at a time when the business might arguably be insolvent (such as CBILS loans, VAT Deferral and Time To Pay arrangements).
Given the level of ongoing uncertainty, is it possible for a director to reasonably conclude that the business will be able to recover and meet these new commitments in full post-pandemic?
As a consequence, trading on and incurring further debt to do so carries significant personal financial and reputational risk for directors.
What does it mean?
Logically, wrongful trading provisions have been relaxed temporarily given that much of the government support in response to COVID-19 will necessarily mean the company is increasing its liabilities.
This will provide comfort to directors acting in good faith and in creditors’ interest, and help them access emergency Government funding without personal liability (save for any personal guarantees) as they navigate the coming months.
Helpful – but not carte blanche
The measures above are intended to help directors and businesses that are trying to do the right thing in exceptional circumstances.
However, it is possible to see how a relaxation of wrongful trading and a longer moratorium might be open to potential abuse from unscrupulous directors, stymieing creditors reasonable expectations of payment, for example.
All other statutory obligations and fiduciary duties of directors remain in force. The temporary “relaxing” should not be seen as carte blanche to act without due consideration or reasonable skill and care; or to take on additional debt without fully understanding the potential consequences to:
- them (personal guarantees)
- the business (such additional debt service costs and a weaker balance sheet) and
- creditors (who may be put in a worse position).
A failure of a director to do so will still carry significant risk as there remain many potential actions through which creditors can seek financial recourse.
Creditors (including employees, key suppliers and lenders) will be hard pushed to support any restructuring proposal if they suspect they are disadvantaged in some way.
Now more than ever, it is critical for directors with solvency concerns to seek timely advice to ensure they are not exposing themselves and their businesses to undue risk or putting creditors in a worse position than they would otherwise be.
If you would like to know more about how our team can help you through some of these challenges and choices, please contact Matt Howard.
Improving your capital structure
10 November 2021
We discusses that there is no magic formula for the right blend of debt and equity in a business – the answer to that depends on the nature of the business, its operations, growth strategy and where it is in the business life cycle. Below, we look at how access to capital has shaped over the last 18 months and what this means for businesses.
Coronavirus Government support schemes
The level of Government support in terms of loans and furloughing during the last 18 months has been unprecedented and without it a lot of businesses would have failed. It has been necessary and it has been good for businesses. Where we’ve tended to seen it operate most is in the smaller entities – looking at the level of borrowing between Bounce Back Loans, CBILS and CLBILS, it’s significantly skewed toward those accessing the bounce back scheme. Our key concern with this is how do those that probably had more limited resources to start with (and now probably have more debt on the balance sheet) manage going forward in terms of their capital and funding? Everything they can do to fund those loans off their own balance sheet will improve their financial position.
With regard to going forward, the Recovery Loan Scheme (RLS) will give many a further comfort blanket and hopefully enable businesses to really push forward and take us through to the next period when people will likely need to tighten their belts. If businesses can access RLS funding to support their recovery into growth, then great. However, what we should point out here is that it should never be used as a sticking plaster for operational issues. All these forms of Government support are debt, they are not grant money, it will have to be repaid in the same way as most commercial debt. Yes, there has been a soft view and easy access to this money, but it does need to be repaid and therefore making sure you’re in the best place possible to generate profit in the future and meet debt obligations is vital.
Debt
The banks have been incredibly supportive alongside the government during the pandemic. Where previously we’ve seen some quite stressed relationships, a lot of clients feel like they’ve had good support from their banks. At the same time, with banks being very supportive to existing customers, there has been more caution around taking on new customers. In particular, if an established business is coming to a new lender for a funding line their first question is why your existing lenders aren’t providing the capital; there must be an underlying reason for it and they’re quite sceptical. We would always advise to go to your existing lenders first before going to a new lender, even in the case of accessing some of the Government support schemes, as they may be able to offer you more competitive terms. However, if you are in the situation of approaching new lenders, then the more prepared you can be to both 1) field their scepticism, and 2) provide evidence for why the funding is needed, what it will be used for and the business’ valuation creation strategy, the better.
There is a lot of discussion already about interest rates and inflation rates over the coming months, and there’s no doubt we will start to see inflation coming in. What this will mean for businesses, particularly those experiencing lower growth and lower profitability is that margins will be getting squeezed which will have a further impact on profitability. While we see a need to start funding more businesses through debt and funding working capital for growth, the other side of the coin is that we’ll see a reduction in margins and profitability to meet that. It may also mean that existing facilities just aren’t providing businesses with what they need to allow growth. In these circumstances, one of the things we always consider as advisors is whether there are different lending structures or options that could maximise a lender’s ability to provide funding e.g. cash flow lending vs. asset based lending (ABL). Businesses that have high revenues but low profitability tend to require a lot of working capital and are therefore are usually better suited to an ABL fund line, rather than cash flow. Having these conversations and seeing whether there are better options available via your lender may unlock much needed capital support.
There is definitely a lot of caution and expectation among banks that they’re going to see increased chances of default, and while there is quite a lot of support and changes around legislations to stop businesses going into insolvent positions, we’ll still likely see a lot of rigour going into bank’s approaches to lending and further cautiousness (particularly if some of those businesses that have accessed government support do default). Therefore, our advice is to ensure you are really clear and prepared from the outset with the information you lender will need in order to enable them to put funding in place, and that you’re prepared if you have to go through any kind of pre-lend review or due diligence via their accountants. Ultimately, you need to be able to prove and evidence to lenders why you need the money you’re asking for and that you’ll be able to fund it – so having a clear strategy, having a clear set of forecast financials that demonstrate that and demonstrate how you’ll repay is vital.
Equity
There is a lot of cash in the form of equity at the moment looking for a home. As ever, for those equity investors with dry powder they’ll be looking to understand the quality of the business, the growth opportunity and prospects, the quality of the management team (to the extent of how well they operate and what their point of difference is relative to others in the market), and how sustainable the business and its profitability is. What is important for anyone looking at private equity is to understand what’s the investment proposition going into it (what does the business look like with and without equity), and therefore how much would the value of the organisation improve and how much of that value are they willing to give up. While some of this will be subjective on the basis of what management are willing to give up, it should also be based on data both of comparable deals in the space (to get an idea of cheque size, valuation and stake given) and the business’ longer term funding plan and expected use of other instruments such as EMI schemes and share options as these will all incur further dilution that investors (and existing shareholders) should be fully aware of going into this round. Secondly, it is also important to consider what you need from an investor both now and in the future, and in terms of cash and relationship, as that can have an important bearing on who you go to for investment. For further information, access our article on business planning here.
Increasing competition for Private Equity
We’re seeing large corporates with improving balance sheets and cash positions, but lower growth rates – these circumstances are creating a perfect environment for these corporates to turn to acquisitions for growth and we are certainly starting to see businesses come back into this market.
We are also seeing a lot of overseas money, in particularly US investment, coming into the UK both from private equity and US private equity backed businesses coming to the UK for opportunities to acquire and invest in their own growth into the UK.
It will be interesting to see how UK private equity will respond to this increased competition for opportunities. However, for those businesses looking for investment this increased competition hopefully results in increased and, perhaps, unexpected options on their own growth moving forward.
There’s a hope in the community at the moment that with all the support that’s been provided to businesses from debt that the route back to growth for businesses and the economy is through equity. During the events of the last 18 months, we have seen private equity firms put more behind their existing portfolio, both in terms of management time and funding, which has resulted in some capacity restraints to look for new opportunities. However, anecdotally, we are certainly seeing them now come back on the ‘looking for opportunities’ trail, so there may be increased opportunities for businesses requiring equity as the world returns to normal.
This article was written by Phil Sharpe, a partner in the SCF team. If you believe you’d benefit from reviewing your capital structure but are unsure of where to start, or have done a review and want to know how to move forward, then please contact Price Bailey’s Strategic Corporate Finance team using the form below.
Automation, accuracy and efficiency, even more critical in the post pandemic environment.
A colleague of mine when discussing cash flow, once used the great analogy of a business being an engine and cash, the fuel that powers it.
A really nice analogy, and one that works on a number of different levels. Just like an engine, a business uses more ‘fuel’ when it is just starting up or accelerating (moving forward / growing).
Engines use most fuel when powering a vehicle over rough terrains, such as an uphill climb or a journey through boggy marshland. For many management teams, the pandemic and post-pandemic trading environment will be the most difficult terrain they have ever faced and hopefully ever will.
In August 2020 the UK officially entered the steepest recession ever recorded. Most economists and industry leaders believe we are not through the worst and that businesses face more challenging terrain ahead and unfortunately probably a steep uphill climb.
The pandemic affected all businesses differently, some were forced to shut overnight others were able to trade but at a reduced level, often at a loss, and a fortunate few relatively unaffected or even benefiting from the pandemic.
The government’s relief packages hopefully provide the UK economy with a ‘rolling start’, reducing the overall impact of the pandemic but also allowing them to recover more quickly.
Interestingly, a lot of businesses we work with seem to have been in that middle ground, operating but at a reduced level, and some are seeing positive results with profits upon budgets and improved year on year comparisons.
In most instances, the improving profits are from management teams consciously reviewing discretionary spend and cutting costs accordingly. We have seen a reduction in marketing and R&D spend, as well as many seeing a reduction in office and travel costs. The use of government reliefs such as rates holidays, grants and the Job Retention Scheme, for many, have provided welcome cash injections.
Management team’s quick actions have meant many indirect income-generating staff, such as admin or marketing teams have been furloughed. This is of course only a short term solution and detrimental in the long term. These costs are easily cut for a short period but it is likely to be unsustainable in the long term with a possible impact on brand awareness or compliance.
This then begs the question, what happens when these reliefs aren’t available? When the furlough scheme comes to a close, rate reliefs end and tax deferrals are due to be paid; just as capital and interest payments are due to begin to repay Business Interruption and Bounce Back loans?
One thing is certain, cash flow management is going to be absolutely crucial in this period so management teams should review their outgoings, stay close to their credit control functions and complete enhanced due diligence on new clients. Late payment and bad debts can cause huge disruption to a business’s cash flow. Statistics show that unpaid invoices in the UK rose by around 200% due to the pandemic. At its peak at the beginning of May 43% of invoices were outside of their contracted terms; meaning a huge amount of money is caught up in the ‘credit cycle’.
With businesses trying to hold on to their cash as long as possible and reduce their working capital cycle, it is likely credit terms will be stretched with payments to suppliers being delayed where not pro-actively chased.
My team and I specialise in helping businesses to adapt their systems and processes to be more efficient and to use the latest technology available to automate tasks allowing resource to be better utilised.
We are seeing a huge amount of businesses adapting to the post-pandemic landscape by outsourcing many different areas of their business. Outsourcing brings with it flexibility, agility and access to a superior skill set. My team can allow you to either outsource your full (/or part of) your finance team; be it the day to day record keeping, payroll or credit control.
By introducing automation to the business’ processes we can offer a complete service which is often more cost-effective but also provides flexibility as the business needs change.
As part of our Virtual Financial Controller Service we can provide real-time data capture and processing, allowing us to produce management reports and analysis on a timely basis as well as cash flow forecasting so that business owners and management teams can closely monitor the business’ financial position, performance and future outlook.
As a direct response to the pandemic fall out, we have introduced our automated credit control service. A low cost but highly effective service, undertaking your normal credit control functions such as issuing statements, invoice chasing ensuring you are on the top of the ‘to pay’ list, and importantly providing credit risk analysis on possible new customers.
Together with our existing credit control service and Escalate dispute resolution and debt recovery service, we are able to offer complete debtor management and collection solution, suitable for all businesses.
Hopefully, it’s not long until we get back to some form of normality, and the outlook looks far more economic!
This blog was written by Lee Sharman, Senior Manager, Outsourcing. To understand more about how outsourcing your finance function can benefit your business, or for support in negotiating the post-pandemic economic environment please contact Lee Sharman or your regular contact at Price Bailey using the form below.
Charity support
The Charity Governance Code 2020 refresh: key changes
Background
The global Pandemic has significantly affected the charity sector, whereby many trustees are prioritising safeguarding cash flows and maintaining charitable activities during a lockdown, in times of increasing demand and constraints on resources. Despite economic uncertainty, effective governance and skilled trustees making informed decisions are crucial ingredients to ensure charities maximise the fulfilment of their aims and objects. The Charity Governance Code (the Code) is an important resource assisting charities to develop high standards of governance and many charities are turning to the Code to help them consider best practice and improved governance in their organisations.
The Code outlines the principles and recommendations for good governance and was created by a sector steering group. The Code is made-up of the following seven principles:
- Organisation purpose
- Leadership
- Integrity
- Decision-making, risk and control
- Board effectiveness
- Equality, diversity and inclusion
- Openness and accountability
Refresh
In an ever-changing world, the Code’s steering group recognise the importance of evolving the Code where required to ensure it continues to be fit for purpose.
Following feedback from an extensive consultation process, the refreshment of the Code in December 2020 focuses on enhancing Principles 3 (Integrity) and 6 (Equality, Diversity and Inclusion), which occurred as these principles received the most consistent feedback concluding amendments were required.
The Integrity principle
This principle has been updated to emphasise the importance of applying ethical principles to decision making, and ensuring a welcoming and supportive culture is embedded into the charity’s values.
The rationale significantly refocuses from the primary concerns of protecting charitable assets and reputation and now additionally highlights culture, values and the right of everyone to be safe. Key outcomes now include:
- Ensuring Trustees understand their safeguarding responsibilities
- Ensuring everyone in contact with the charity is aware of how to raise concerns
- To address power imbalances/conflicts of interest where they exist or arise
- To establish appropriate procedures, which are integrated with risk management and training
Thus embedding the values, ethics and culture of the charity into everything it does and its decision making – the personal behaviour of Charity Trustees for instance is paramount which has been clarified in the Code.
The equality, diversity and inclusion (EDI) principle
The ‘Diversity’ principle name was renamed ‘Equality, Diversity and Inclusion (EDI)’ principle following consultation conclusions that the principle should be reworded to work towards inclusive cultures as well as Board diversity.
Effective EDI is considered a journey and sits at the heart of good governance. The rationale of principle 6 is to aid boards to maximise public benefit, redesign their charitable purpose where necessary and make robust and informed decisions. The EDI principle now recommends Boards to consider the following four stages of practice:
- Assessing an understanding of EDI and considering why it is important for the charity to consider.
- Formulate context-specific plans and targets and assess the charity’s starting point.
- Taking action and monitoring EDI performance.
- To be transparent and learn from progress to date.
Final considerations
The Code’s principles, rationale and outcomes are considered to apply to all charities regardless of size or activities. Governance practices can differ significantly depending upon a charity’s activities, complexity, income or size; different versions of the recommended practice have therefore been published to address some of these differences, split between ‘larger’ and ‘smaller’ charities.
It is worth noting that some of the principles and recommended good practices set out by the Code are deliberately aspirational, and a stretch for many charities to achieve. This is intentional, as the steering group want the Code to be a tool for continuous improvement towards the highest standards.
The full Charity Governance Code, along with additional information, can be found here.
This post was written by Simon Rowley, Manager and charity sector specialist at Price Bailey LLP.
COVID-19 and its effect on VAT recovery for charities
In many cases, COVID-19 has changed not only the overall value but also the relative composition of a charity’s income. Therefore, this may have implications on the charity’s VAT recovery due to the partial exemption method calculations and the annual adjustment.
For VAT registered charities that need to restrict their VAT recovery based on a partial exemption method, this change could impact the amount of overhead VAT they can recover as most recovery calculations are based on income. For example, retail sales declining relative to grant income could mean more non-business and less recovery. In contrast, sponsorship, increasing relative to exempt admission income could mean a higher recovery. There will be winners and losers.
VAT recovery calculations are normally finalised at the end of your VAT year that ends in January, February or March. We recommend that you estimate the impact that COVID-19 has had upon your VAT recovery now, before undertaking this annual calculation. This is because if your recovery has been detrimentally affected, it might be possible to seek a special recovery method from HMRC. This usually will need to be applied for before the end of the current VAT year. If you predict your VAT recovery percentage will fall as a result of COVID-19, get in touch, especially if you have an open capital goods scheme item.
This article was written by Helena Wilkinson, a charity specialist and Partner at Price Bailey. If you have any questions on how your VAT recovery might be impacted, you can contact Helena using the form below.
Employment law support
Why redundancies might not be your only option
As the Government’s job retention scheme is scheduled to come to an end in March 2021, many employers are now considering what their workforce will look like going forward and if redundancies are going to be needed.
In these circumstances, making employees redundant is an obvious option for reducing costs. However, making redundancies is a real loss for businesses. Not only is it expensive, but it often means letting go of good people who employers have invested in and may not easily be replaced.
However, if there is a possibility of an upturn in the short to medium term, retaining employees may be the best approach.
How can you retain employees?
- Job Support Scheme – To make use of the Government’s Job Support Scheme, employees must work and be paid for 20% of their normal hours. For every hour not worked, the employee will be paid up to two-thirds of their usual salary. The government will provide up to 61.67% of wages for hours not worked, up to £1541.75 per month (more than doubling the maximum payment of £697.92 under the previous rules). The cap is set above median earnings for employees in August at a reference salary of £3,125 per month. You can find out if an employee is eligible for the scheme by using our online calculator. If an employee is eligible, employers must have a written agreement with their employees regarding the Scheme. HMRC have stated this agreement must be made available to them upon request. If an agreement cannot be produced, HMRC may demand that all financial support offered under the Scheme be repaid by the employer. In addition, failure to agree on the reduction in hours with an employee properly may result in an unlawful deduction from wages claim.
- Job retention bonus – Review whether there is any other government assistance available. For example, having regard to the Government’s job retention bonus, if you know you are going to retain at least some of your furloughed employees after January 2021, does the benefit of being paid £1,000 per furloughed employee enable you to keep on some other employees who you may otherwise make redundant?
- Reducing overheads – Carefully review your company’s overheads and gain control of your spending to see whether you can make sufficient cost savings before looking to reduce your headcount.
- Pay freezes – this will be unpopular for many reasons, but as an employer, your primary commitment should be to preserve employment for as many people as possible – stopping a pay rise is a good way to manage cost and maintain employment for the majority.
- Reducing salary or hours – Agreeing with employees to reduce their salary or hours – this approach has the same purpose as redundancies (i.e. reducing costs). Yet, it doesn’t require you to let employees go. An additional benefit to this approach is that when business eventually picks up, you still have a full workforce and don’t have to spend time and money recruiting new employees. However, you cannot just change an employee’s terms of employment without their consent. Changing terms of employment needs to be done correctly; otherwise, you risk exposing your business to claims and costs, which could ultimately defeat the purpose of making the changes in the first place. It is, therefore, advisable to seek legal advice before making any changes.
If you have to consider redundancy, make sure you follow a fair process.
If, after considering all avenues, you may find that, unfortunately, redundancy is your only option. During these unprecedented times, it is essential to ensure that you follow a fair redundancy procedure as the financial risks of getting things wrong can sometimes be very significant. To guide you through this process, we have put together a Redundancy Support Hub.
Alternatively, if you would like to discuss with us your redundancy proposal please get in touch.
This article was written by Claire Berry, an Employment Solicitor at Price Bailey . If you have any questions or require any assistance, you can contact Claire and the employment team on the form below.
How to manage a safe return to the workplace and some frequently asked questions
Following the Prime Minister’s unveiling of a roadmap out of national restrictions, businesses will be beginning to take steps to welcome their teams back into the workplace.
It’s a certainty that life with COVID-19 will continue to evolve around us, but regardless of what the next few months hold, it’s important that you take the time to plan and work with your employees to establish the new ways of working.
Key steps to take:
- Consult with your employees as early as possible about returning to the workplace
You should consult with employees before making any final decision or putting plans in writing. Points to discuss include:
- Sharing the vision about the future of the workplace, what this will look like and any plans for hybrid working (see point 3 for more detail on hybrid working patterns)
- when staff might return to the workplace
- how staff will travel to and from work
- how health and safety is being reviewed and managed – you should share the latest risk assessment
- any planned adjustments to the workplace, for example, additional handwashing facilities, staggering start and finish times to avoid overcrowding or floor markings to help people stay apart
- if there might be a phased return of the workforce, for example, some staff returning before others
- Make the workplace Covid-19 secure
All employers have a statutory duty to provide a safe place of work and general legal duties of care towards anyone who may be accessing or using their place of business. To discharge these duties, you must take the following steps:
- Carry out suitable risk assessments to identify the risks; and
- Implement measures to minimise those risks. You must take all reasonably practicable steps to minimise the risks. This is not the same as having to eliminate the risks, although.
To clarify what you need to do, you should refer to the relevant sector-specific guide contained in the government’s guidance on working safely during coronavirus www.gov.uk/guidance/working-safely-during-coronavirus-covid-19. It must be read in conjunction with other health and safety laws and regulations and any advice produced specifically for your sector by industry bodies.
- Ensure that your employment documentation is up to date
Evidence suggests that as restrictions ease, a majority of employers are considering a ‘hybrid’ pattern of working, involving both home and workplace-based work rather than full return to the workplace. In such cases, you will need to formalise homeworking arrangements, update your employment contracts, and put in place homeworking/ hybrid working policies.
You may also need to review your staff handbooks or individual policies and procedures to ensure that they are applicable to and support any new ways of working that have been introduced as a result of COVID-19. Policies that may have been affected include sickness, absence and pay, health and safety, disciplinary offences and harassment and bullying.
Frequently asked questions
What happens if someone does not want to return to the workplace?
It is ultimately an employer’s choice as to whether you require your employees to attend work; however, you should follow government guidance.
Where you can demonstrate that you have taken all reasonable steps to minimise the risks, it may be reasonable to insist an employee returns. If they refuse to, it could result in a disciplinary issue. As each case is fact sensitive, it is important that you take legal advice before taking further action.
Should we be carrying out workplace testing?
There’s no law that says that businesses must test employees for COVID-19, and in most situations, it is not necessary, but some employers might want to bring in testing as part of their workplace policy. If you do decide to introduce workplace testing, it does not mean that you can reduce other COVID-19 secure workplace measures already in place.
Can we insist on workplace testing?
Where an employee is exhibiting symptoms of COVID-19, it may be reasonable to require that employee be tested, where the purpose of the testing is to protect the health and safety of the workforce.
The situation is more complicated when employees are not exhibiting symptoms. If an employee does not agree to workplace testing, they cannot be forced to do so. In certain circumstances, it may be open to employers to take disciplinary action against an employee who refuses a test, but this would depend on factors such as the nature of the employee’s work; any evidence on the necessity of testing in the particular environment and the extent to which the risk of COVID-19 cannot be managed in the workplace by other measures. You should also ensure that you consider the reasons why the employee refused and whether or not these can be viewed as “reasonable”.
What data protection issues arise from workplace testing?
Test results are classed as ‘special category data under the General Data Protection Regulation (GDPR), and as such, there are more stringent conditions for processing it. The fact the employee has consented to being tested or to this information being processed will not of itself be sufficient.
Given the sensitive nature of the data collected, employers must process the data in accordance with the GDPR and inform employees in an open and transparent manner about the reasons for processing their personal data, what decisions will be made as a result of you having that information, which it will be shared with and how long it will be kept for. Employers should consider putting a COVID-19 testing policy in place to help meet this objective.
The Information Commissioner’s Office (ICO) has published guidance for businesses on managing data protection obligations ico.org.uk/global/data-protection-and-coronavirus-information-hub/coronavirus-recovery-data-protection-advice-for-organisations/testing. The guidance makes it clear that employers will need to show that their approach to testing is reasonable, fair and proportionate, taking into account the specific circumstances of their business. It also recommends that employers undertake a “data protection impact assessment” to help them with determining if their approach meets the testing threshold.
Can we ask an employee if they have had a vaccine?
Before you decide to ask your employees about vaccination status, you should be clear about your reasons for doing this. Whether your employee has been vaccinated is their private health information and is, therefore, ‘special category data’, and your use of this data must be fair, necessary and relevant for a specific purpose.
If you have no specified use for this information and you are recording it on a ‘just in case basis, you are unlikely to be able to justify collecting it if you are challenged in the Employment Tribunal. The sector you work in, the kind of work your employees do, and your workforce’s health and safety risks should help you decide if you have compelling reasons to record whether your employees have had the vaccine. It is likely to be easier to justify collecting such information in certain workplaces such as a health or care setting where COVID-19 presents a specific risk.
If you carry out a “data protection impact assessment”, as we explained above, you will start to formalise the reasons why you are collecting this information.
If you decide that you can justify recording whether employees have had the vaccine, you must be transparent. You must make sure that your employees understand why you need to collect this information and what you’re using it for. You should accurately record the information that you collect and ensure that this is stored securely. You should regularly review whether you still have grounds for keeping this information as the vaccination roll-out progresses and more people receive the vaccine.
If we make a reasonable request for employees to be vaccinated, what can we do if they refuse?
There will be employees who are unable or unwilling to have the vaccine for a wide range of reasons. This may be because of a medical condition that prevents them from being vaccinated. It may be for religious reasons or for reasons of philosophical belief, or they may have concerns about the safety or effectiveness of the vaccination.
If employees do not have a valid reason for not having the vaccine, as an employer, you could argue that a request to be vaccinated amounts to a reasonable management instruction, and failure to follow an employer’s reasonable instructions can lead to disciplinary processes and dismissal.
Whether a requirement to be vaccinated is a reasonable management instruction will depend on the specific circumstances at the time. For example, employers in the healthcare sector may potentially be able to issue a reasonable instruction to employees to be vaccinated because refusal could put vulnerable patients at risk. However, employers in another sector, where work can be done effectively from home, maybe in a weaker position to argue that an instruction to be vaccinated is reasonable.
This article was written by Claire Berry, a solicitor at Price Bailey. If you have any other questions about staff returning to work, you can get in touch with Claire on the form below.
End of plan B: Return to offices
Following the end of Plan B, employers’ attention turns once again to what they want long-term working arrangements to look like, with many opting for remote working to be required or accommodated, on either an exclusive or partial basis.
Whether hybrid working is practicable and, if so, how it will work will depend on the nature of the business and the individual’s role and circumstances. Some jobs can be carried out remotely, whilst others, particularly those that are client-facing, would not be.
Whatever the agreed arrangement is going forward, it is important for employers to update contracts to reflect and formalise the new working arrangements, and to be aware of (and to address) several practical issues that come with hybrid working/home working.
Where contracts are amended to reflect the employee’s home as the place of work, employers will need to retain some flexibility to deal with some of the practicalities. For example, requiring employees to attend the office for training, appraisals, or disciplinary issues and dealing with how expenses for travel to and from the office should be met. If an employee moves house, this may mean higher travel expense claims, or a practical barrier to attending work at the office – so employers could consider placing limits on how far an employee can move from a particular location.
Employers may also want to retain the flexibility to alter the arrangement temporarily and consider making the agreement to homeworking conditional on certain conditions being met such as satisfactory performance being maintained. Unless employers are confident that hybrid working/ homeworking is the right approach, it would be sensible to build in a trial period and review the arrangements.
Addressing these issues at an early stage will help employers to avoid future pitfalls and risks, such as employees refusing to comply with specific requirements that are appropriate under the type of working model which has been applied to them.
It is also advisable for employers to develop hybrid working and home working policies that sit alongside the contract of employment. This might set out the employer’s commitment to encouraging hybrid working/ home working, how such arrangements will operate, and the expectations of employees and managers. Employers may also need to modify other policies such as IT, expenses, confidential information, and data protection to address any specific points regarding hybrid/ homeworkers.
It is also an important time for employers to review their HR processes and procedures to ensure they support remote working in practice, and to ensure that managers receive training on how to manage teams effectively and support home/hybrid workers, including;
- performance management
- remote communication
- collaboration
- relationship building
It is also important to treat all employees fairly and equally and everyone should be given the same access to work, support and opportunities for training and promotion.
Equipment
If hybrid working is to be a success, it is important that employees have the equipment they need to perform their role. Disabled employees may be entitled to auxiliary aids as a reasonable adjustment. If such an aid is reasonably needed, employers should make sure it is provided at their expense, although they may be entitled to support from the Government’s Access to Work Scheme.
Property and insurance
Employers are required to have employers’ liability insurance and should tell their insurers that they have employees working from home. Employers may also want to check that their business insurance covers their property when in employees’ home (for example laptops provided to support homeworking). If employees have home insurance or a mortgage, they should be advised to tell their insurer or lender that they are working from home in case it affects their cover.
Health and safety
Employers have duties relating to the health and safety of employees, this includes mental and physical health, which apply even if they are working from their own home. If employers are putting in place more permanent homeworking or hybrid working arrangements, it is likely that they will need to revisit any health and safety risk assessments that were carried out as part of homeworking during the COVD-19 outbreak, as different considerations will apply where homeworking is being allowed on a permanent basis compared to a temporary one.
Employers will also need to address health and safety issues in the context of homeworking and hybrid working including providing appropriate first aid provisions and supplies; ensuring there is a reporting procedure for accidents wherever they occur, and making sure that all workstations meet the requirements laid down.
Data protection and security
As an employer, you have a duty under data protection legislation to use appropriate measures to ensure the security of personal data and to protect it from unauthorised processing and loss. This applies to personal data in an employee’s home. Employers should also carry out a data privacy impact assessment. Some of the measures that you may decide to take to protect personal data include:
- Ensure that only the employee has access to personal data on the device and that other members of the household do not have access. In practice, the best approach is for the employer to provide the device.
- Encrypt the device or permit the employee to password protect personal information.
- Centrally control updates to software, security, password changes and the capacity to wipe the device remotely.
- Apply rules on the proper disposal of paper-based records, for example shredding.
- Provide guidance and training on the procedures to be followed and what is, and is not, an authorised use of personal data.
There are many points to consider when formally implementing hybrid working. If you have any questions on the points raised in this article or would like assistance with updating employment contracts and policies/ procedures, please contact us at employmentlaw@pricebailey.co.uk.
A Q&A on employment tribunals during COVID-19
The Employment Tribunal has adapted its usual practices to adhere to government guidance on social distancing and other COVID-19 measures. To clarify things, the Presidents of the Tribunal have released a Q&A of the key questions that they have encountered since these measures came in to force. We have set out below the most relevant points to note.
Postponed hearings and preliminary hearings
Hearings due to take place up to 26 June 2020 have been rearranged to preliminary hearings, to be conducted by telephone. Some people have asked if it is possible to continue with the face to face Hearings previously planned, but “No” this is not an option. Hearings due to take place after 26 June have not yet been revised or postponed; however, it is essential to look out for any changes in the arrangements of your Hearing as the advice surrounding COVID-19 develops.
The Tribunal will notify you of a rearranged hearing, the Tribunal is dealing with a high volume of communication, so there is a chance that you will only receive up to a weeks’ notice.
These are some top tips to help you prepare for a preliminary hearing by telephone:
- Make sure you have the appropriate equipment – Laptop/smartphone/internet connection where necessary
- Join the call/video early and wait for the Judge to conduct proceedings
- Use chat panels if available to indicate when you wish to speak. Put your microphone on mute if you are not speaking.
- Find the right setting – make sure you are somewhere quiet and private. If you have a video conference, make sure you consider and test the picture quality, and don’t forget what is in the background of the video. You might even be able to blur the background.
Q: What if you can’t attend a preliminary hearing?
A: You can email the Tribunal to explain your circumstances and request to rearrange, whether it is due to illness, or you feel that adverse conditions are preventing you from adequately preparing for a Hearing. Mark the email as Urgent in the subject line. It is at the discretion of the Tribunal whether or not rearrange the Hearing.
Q: When will postponed cases be rearranged for?
A: It’s impossible to give an exact timeframe for this. Certain case types are being dealt with as a priority: Statutory appeals against prohibition notices, Applications for interim relief and Dismissals where an individual has lost accommodation tied to their employment.
Q: What about Judicial Mediations due to take place 26 June 2020?
A: Mediations are still planned to go ahead, but via video conferencing facilities such as Zoom, Skype for Business or MS Teams. Keep the points above regarding preparation in mind ahead of the conference.
Deadlines and time limits
Q: Will time limits be extended?
A: No they will not be. Time limits relate to the deadline that you need to stick to when submitting your claim to the Tribunal or to Respond to a Claim made against you. These time limits are not set by the Tribunal. If party to a claim does not act before the time limit is reached, this will be assessed on a case by case basis, but there has been no change to the time limits, so they must still be complied with.
Q: Do I still need to comply with Orders, even if they are to be actioned before 26 June 2020?
A: If the Orders were made prior before the 23 March 2020 and relate to a Hearing due to take place before 26 June 2020, then No.
If they relate to a Hearing due to take place after 26 June 2020, then Yes, you should still comply with these Orders.
Tribunal opening arrangements and contacts
Q: Can I ask the Tribunal to contact me at another address – i.e. if I am working from home?
A: Yes. With people working remotely the original contact details provided might not be the best way for the Tribunal to correspond with you. You can ask the Tribunal to contact you at a different address, for example a shared mailbox or alternative postal address.
Q: Is the Tribunal open?
A: Yes the Tribunal offices are remaining open. There have been temporary closures where this has been deemed necessary, but in general the Tribunals are open.
Q: How should I contact the Tribunal?
A: You can contact the Tribunal by phone, email and post. The Tribunal recommends contact by email to avoid unnecessary phone calls. You can also hand deliver paperwork to the Tribunal.
The Tribunal asks for your patience during this time, they are operating with reduced staff numbers so there will be delays when responding to correspondence and processing paperwork.
When communicating via email If the correspondence needs attention urgently please type “Urgent” at the beginning of the subject of the email, followed by your claim number and the names of Claimant & Respondent.
Keep an eye on these links for updates directly from the employment tribunal
This post was written by Heidi Berry a Lawyer at Price Bailey, for more information contact, Heidi on the form below.
COVID 19 Employment Tribunal cases on the rise
The Employment Tribunal is starting to give decisions on claims brought at the beginning of the COVID-19 pandemic. As both employers and employees, we have all learned a lot about how to handle the various challenges that have arisen over the last year, and we are now starting to gain an insight into how the Employment Tribunal perceives and interprets the way that employers have handled these challenges.
This blog will look at a recent Employment Tribunal decision that shows the importance of employers implementing robust COVID-19 measures, policies, and procedures to protect themselves from several costly claims that an employee could make.
The case under the microscope in this blog is Rodgers v Leeds Laser Cutting Ltd ET1803829/2020 (1 March 2021). Mr Rodgers brought a claim for automatically unfair dismissal against Leeds Laser Cutting Ltd. Mr Rodgers notified his employer that he would be staying away from the workplace to protect his family’s health in light of the growing COVID-19 threat and would stay away until the pandemic was over. One month later, Mr Rodgers was dismissed from his employment. The case presented by Mr Rodgers to the Tribunal was that he was automatically unfairly dismissed because he was entitled to stay away from his workplace where he believed there was a risk of serious and imminent workplace danger. This is an exercise of his right under s.100(1)(d) and (e) of the Employment Rights Act 1996 (ERA 1996).
The Tribunal found in favour of the Respondent that their decision to dismiss Mr Rodgers was not automatically unfair and that he had failed to prove that there was a genuine belief in the severity of the danger that he would be exposed to if he had continued to attend his workplace throughout the pandemic.
We want to highlight why the Employment Tribunal reached this decision. Their reasoning is based on the specific facts and circumstances at the time of Mr Rodgers dismissal.
- He had breached his self-imposed isolation by taking a friend to the hospital.
- His employer was following all the relevant government guidance in force at the time.
- He had not made any prior efforts to avoid the danger that he felt he was exposed to at his workplace.
Employees have a duty to make themselves available for work and accept instructions and tasks from their employer. Employers have a duty to ensure that the workplace is safe for their employees. In this case, Mr Rodgers leaned on his belief that attending the workplace was detrimental to his health and safety. The Tribunal recognised that the employer had taken all reasonable steps to create a safe workplace and that the employee’s actions contradicted the severity of his perception of the danger he was exposed to. Please note that this decision is not binding and turned on the specific facts.
As cases such as this reach the public domain, more employees will probably look to assert their right under s.100(1)(d) and (e) ERA 1996, particularly now that more employers are asking their employees to return to the workplace. So our message to employers is that they communicate clearly with their employees what steps are being taken to minimise the dangers posed by the pandemic. The best way to do this is to implement a COVID-10 policy and provide regular updates to the workforce on the specific measures in place.
Another type of claim expected to increase is whistleblowing. Employers must take all comments and feedback on their COVID-19 policies and measures incredibly seriously. Failure to do so may line an employee up to bring a successful whistleblowing claim. Where it is projected that whistleblowing claims concerning defective or non-existent COVID-19 policies are likely to be on the rise, we want to encourage all employers to take the time to review the policy documents that they have in place to avoid the costly repercussions of an avoidable employment tribunal claim.
Our legal services team can help you review the measures and policies you have in place and provide new policies if you haven’t yet put something in place. Get in touch with the team via the form below.
Living with Covid-19 and advice for employers
From the 1 April 2022, those with Covid-19 are encouraged to exercise personal responsibility in line with the Government’s Living with Covid-19 in England plan.
Following the phasing out of self-isolation legislation in favour of government guidance and advice, employers are being forced to determine and examine how they will deal with Covid-19 and whether they will apply any of their own rules or policies in their workplace.
Employers in England are having to find a balance between living with Covid-19 and their responsibility to create a safe workplace.
What changes have been made?
As of 24 February 2022, employees were no longer required to self-isolate if they tested positive for Covid-19, or if they have been in close contact, regardless of vaccination status. However, the Government strongly advised people to self-isolate for five full days, and until they received 2 negative test results on consecutive days.
From 1 April 2022, Government guidance is now focused on encouraging people who have symptoms of Covid-19 – or have received a positive test result – to exercise greater personal responsibility, try and stay at home, and avoid contact with others. This is in an attempt to protect those who are most at risk from Covid-19.
SSP
• Those with Covid-19 may still be eligible for Statutory Sick Pay (SSP) subject to the normal conditions of SSP. Employees can receive SSP from the fourth day they are off sick, and when needed must provide you with notice and proof of illness. SSP will no longer be payable to employees who test positive but are not incapacitated, nor to any self-isolating close contacts.
Testing
• As of 1 April, free symptomatic and asymptomatic lateral flow (LFT) and PCR tests have ceased but care home residents, hospital patients, and other vulnerable groups will be given free tests if they have symptoms.
• The Government is working with retailers to ensure that everyone who wants to can buy a test. Some high-street pharmacies are selling individual LFTs from £1.89 per test, or a pack of five for £9.29.
Workplace guidance
• The health and safety requirement for every employer to explicitly consider Covid-19 in their risk assessments has been removed as of 1 April 2022. However, employers that specifically work with Covid-19, such as laboratories, must continue to undertake a risk assessment that considers Covid-19.
• The Government will consult with employers and businesses to ensure guidance continues to support them to manage the risk of Covid-19 in workplaces.
• There will continue to be specific public health guidance for those whose immune system means they are at higher risk of serious illness from Covid-19 despite vaccination.
What are the practical implications for employers?
If there are more people with Covid-19 attending the workplace, this could represent a risk to the company. An outbreak amongst a team could jeopardise the ability to continue functioning effectively.
With free testing being discontinued, it is even more difficult for employers to know if their employees have Covid-19. Bearing this in mind, employers should make sure they are adhering to the Workplace (Health, Safety and Welfare) Regulations 1992, and ensure they have effective ventilation in any enclosed workplaces.
As the focus of the new phase of Living with Covid-19 is to protect those who are most vulnerable, employers should consider encouraging workers to protect others who may be at higher risk. This includes, social distancing, ventilation, and face coverings. However, it is no longer a legal obligation to follow these requirements.
Can employers require people to stay at home if they test positive for Covid-19?
You could consider implementing workplace rules/policy regarding Covid-19. This could require an employee to stay at home if they receive a positive test or have Covid-19 symptoms, and either work from home, or not work at all if they cannot work from home.
It is unlikely that a requirement to work from home or stay at home isolating if test positive or have Covid-19 symptoms could be argued as being unreasonable, unless there is a significant detriment. Therefore, you will have to pay full pay if your workplace policy requires an employee to stay at home but the employee is physically fit to work, and is willing to do so, however, they cannot do their job from home.
What steps should I be taking?
- To reduce the risk of spreading Covid-19 in the workplace you can encourage employees to follow the Government’s advice of trying to stay at home and away from others if they receive a positive test or have Covid-19 symptoms.
- Decide and implement a workplace policy as to what to do if an employee tests positive. This could include decisions on working from home, not working at all, and corresponding pay.
- Employers may wish to consider the needs of employees at greater risk from Covid-19, including those whose immune system means they are at higher risk of serious illness from Covid-19.
- Decide if you would still like to encourage social distancing and wearing a face mask amongst employees.
- Communicating and being transparent with employees who are still reluctant to return to the workplace. Having steps in place that follow Government guidance when an employee tests positive may help to address concerns.
If you have not done so, we strongly advise that employers set out what their policy is if an employee tests positive for Covid-19 or has Covid-19 symptoms and the implications for pay. This should then be communicated to employees so everyone is clear about what to expect.
This article was written by Claire Berry, an employment solicitor at Price Bailey. If you have any questions on the points raised in this article or would like assistance with creating a Covid-19 policy, please fill out the form below.
COVID in the Employment Tribunal – Employee’s dismissal was not automatically unfair.
As a timely follow up to our blog considering the impending rise of Employment Tribunal cases being brought where employees disagree with their employer’s handling of events during the pandemic, the Employment Tribunal has recently delivered another useful decision.
It is important to note that, because this is a decision from the Employment Tribunal rather than a higher court, this is a non-binding outcome.
In Accattatis v Fortuna Group (London) Ltd it was ruled that Fortuna Group (London) were justified in their decision to dismiss Mr Accattatis in April 2020 when he would not accept the options to go on either annual leave or unpaid leave instead of working from home on full pay or going on furlough leave under the Coronavirus Job Retention Scheme for 80% of his normal pay. Mr Accattatis claimed that the decision to dismiss him fell within the scope of automatic unfair dismissal because of his reasonable belief of being in serious and imminent danger. Amongst other reasons, an employee is considered automatically unfairly dismissed if the main reason for their dismissal was because of their taking action, or proposing to take action, over a health and safety issue
Once again, the specific facts of this case guided the ET’s decision: Fortuna Group manufactured PPE, meaning that they were incredibly busy and moreover Mr Accattatis’ role could not be carried out from home. Mr Accattatis had requested to be placed on furlough leave and to receive 80% of his normal pay because he did not feel safe using public transport to travel to work. Where his role could not be carried out from home, his employer agreed that he could stay at home but that this must be as annual leave or unpaid leave. The ET interpreted that Fortuna Group had acted reasonably because they had recognised their employee’s desire to avoid using public transport, but that they were also reasonable in declining the request to work from home or utilise the CJRS furlough scheme because there was no reduction in demand for Mr Accattatis’ role and this role could not be carried out from home.
We think that this case is particularly interesting for employers because it reiterates the importance of interpreting government guidance accurately and fairly. Fortuna Group had acted entirely reasonably, in the view of the ET, by preventing Mr Accattatis’ access to the CJRS. The ET viewed Mr Accattatis’ intent as motivated more by financial gain than his need to subvert the imminent danger posed by COVID-19 if he were to continue using public transport. The CJRS was established to enable businesses experiencing a downturn to survive and for employees to retain their jobs if their role was temporarily reduced or not required as a result of the pandemic. Furthermore, the ET explained that they found in favour of Fortuna Group because of the way that they communicated with Mr Accattatis and sought to appease his perceived danger of travelling on public transport.
It is a testament to Fortuna Group that they acted in accordance with the intentions of the government guidance and were not swayed by the pressure created by Mr Accattatis’ persistent requests to access the CJRS. At times it can be difficult for employers to exercise an unbiased interpretation of the relevant guidance and rules that are applicable to difficult situations arising in the workplace. This is where the professional input of a legal adviser can avoid a costly mistake or equally confirm an important decision.
Our legal services team can help you review the measures and policies you have in place and provide new policies if you haven’t yet put something in place. Get in touch with the team via the form below.
Tribunal rules long COVID to be covered under the Equality act
An Employment Tribunal rules that long Covid sufferer was disabled under the Equality Act- what does this mean for employers?
In the recent case of Burke v Turning Point Scotland, the Scottish Employment Tribunal ruled that an individual suffering from long Covid was ‘disabled’ for the purposes of the Equality Act 2010 (‘Act’) and was therefore permitted to bring a disability discrimination claim against his former employer.
Mr Burke is the first person in the UK to successfully claim that long Covid is a disability. This does not mean that every long Covid sufferer will meet the legal definition of disability, as each case will depend on its own facts.
Facts of the case
Mr Burke was employed as a caretaker by Turning Point Scotland for about 20 years. In November 2020, he tested positive for Covid. Initially, his symptoms were mild. However, after isolating he developed severe headaches and fatigue. After waking, showering and dressing, he had to lie down to recover and struggled standing for long periods. He could not undertake household activities like cooking, ironing and shopping. He experienced joint pain, loss of appetite and inability to concentrate and difficulties sleeping. He also felt unable to socialise.
His symptoms were unpredictable as on some days he felt better than on others. He obtained fit notes from his doctor throughout his absence which quoted ‘fatigue’, ‘after effects of long covid’ and ‘post viral fatigue syndrome’. Two occupational health reports were obtained by Turning Point which stated that he was fit to return to work and that the disability provisions of the Act were unlikely to apply.
However, relapses of his symptoms (in particular, fatigue) meant that he did not return to work. He was dismissed in August 2021 because of ill health and he brought Tribunal claims against his former employer, including disability discrimination. Turning Point sought to have the disability discrimination claim struck out on the basis that his condition did not constitute a disability under the Act. A preliminary hearing was held to determine this point.
Was Mr Burke disabled under the Act?
A person is disabled under the Act if they suffer from a physical or mental impairment which has a substantial (i.e. more than minor or trivial) and long-term effect (has lasted or is likely to last at least 12 months) on their ability to carry out normal day-to-day activities.
Applying these principles to this case the tribunal found that:
- Mr Burke had a physical impairment (long Covid/ post-viral fatigue syndrome), and his fluctuating symptoms were consistent with a June 2021 TUC report regarding workers’ experiences of long Covid;
- His physical impairment had a substantial effect on his ability to carry out day-to-day activities;
- This effect was long-term because it ‘could well’ be that it would last for a period of 12 months when viewed from the dismissal date, which was the last alleged discriminatory act;
- He was not exaggerating his symptoms. There was no incentive for him to remain off work when he had exhausted sick pay;
- The lack of particularisation of symptoms within initial fit notes could be explained by the restrictions on in-person consultations at the time.
Key points for employers to take from this case:
- Be mindful that long Covid may amount to a disability;
- Consider all medical evidence available. If there is any uncertainty, seek further medical advice from the employee’s GP or an occupational health adviser, along with legal advice as, although medical evidence is helpful in understanding an individual’s diagnosis and prognosis, it is not determinative of whether a person’s condition constitutes a disability, that is a legal question to be determined by the tribunal;
- Think about whether and, if so, what reasonable adjustments may be appropriate and consult with the employee on any proposed adjustments.
This article was written by Claire Berry, an employment solicitor at Price Bailey. If you have any questions on the points raised in this article or would like assistance, please fill out the form below.
Fraud on UK businesses continues to rise through the pandemic
As the pandemic continues to play out and impacts the UK economy far more significantly than we ever expected, many fall on hard times; pushing some to commit a crime they would not typically have done.
This article covers some of the main risks to businesses and individuals and provides some of the key, easier to implement, preventative measures. For further information, the Action Fraud website is a library of support for businesses and individuals and allows you to report a fraud both as a victim and witness.
Unfortunately, the main reason for the increase in fraud on UK businesses is the large number of individuals who will use change and uncertain times to exploit people and organisations.
Fraud is more prevalent around key dates and holidays. Fraudsters are more likely to attack when they think the individual or business will be most open; busy bank holidays, busy seasonal periods or simply Friday afternoons when people try to leave the office. Currently, nothing is very normal, businesses are trading at reduced capacity, staff are on and off furlough, and many are completing different roles than they would have previously; all these factors open businesses up to fraud.
There are two main ways to categorise fraud types, authorised and unauthorised. Authorised is where the fraudster tricks the individual into authorising a release of funds into an account controlled by the fraudster. Unauthorised is where funds are taken from an individual or company without their permission and, often, their knowledge.
The first line of defence is knowledge; this article goes some way to explore the most common types of fraud that UK businesses are subjected to.
What are the most common types? And how can you protect yourself, your employees and your business?
Authorised fraud types
We can stop many of these types of fraud with training, process and consideration.
Invoice redirection fraud
This fraud is committed by a fraudster impersonating a company’s supplier, reporting to have amended their bank account details, and asking that all further payments are sent to a new fraudulent account. The account details are that of an account opened fraudulently, the business is often only made aware once the real supplier contacts them requesting payment.
The fraudulent request can be received in many forms; email, phone call or letter. The fraudster will often have done their research and found the named company is a genuine supplier, what they supply, and an individual’s name at the company. They will often make the request via email with a spoof email address or via letter on headed paper.
Prevention
- Educate all staff; letters are often sent to staff not in the finance team, hoping that the letter is left on someone’s desk in the finance team to amend without question,
- Have dual authorisation activated on online banking. That way when a payee’s details are amended, it requires a sign off from another member of staff who can question the validity,
- Implement a process to always complete a call back to a known member of staff at the supplier, making sure not to use a number from the fraudulent email/ letter but one from a readily available source (internet) or preferably a known regular contact number,
- Using technology to automate invoice receipt and processing can be an easy way to prevent this fraud. The systems flag inconsistencies in invoices received which can prevent payments from being made to new account details without prior authorisation,
- The supplier needs to be confirmed as a genuine supplier for the scam to work, so keep invoices safe, out of sight and internet security up to date.
Bogus Boss/ Director/ CEO fraud
This fraud is a regular occurrence, which often preys on the more junior members of the team. There are two reasons fraudsters may use this type of fraud; firstly to get a member of staff to click on a link so that malware may be installed on their system, secondly to request payment be sent to a fraudulent account.
The fraud is committed by impersonating a director/ manager / authoritative figure within a firm; easily found on most websites. The fraudster emails a member of staff, most commonly requesting a payment be made to an account. The email is often sent in an urgent nature confirming the payment needs to be made quickly and for reasons such as; it is for a new client win, the boss is stuck somewhere, or there will be recompense for the individual’s colleagues if not made quickly. This urgency is designed to make people think quickly and not clearly.
The email will often come from a spoof email very much like the directors; these are easily guessed or again found on the website. The fraudster will have often intercepted emails from the director and will mimic the email wording and tone so as not to alert the individual.
Prevention
- Educate all staff, not just the finance team. Emails are often received to random email addresses within the firm. Some will unwittingly forward the email to the finance department; if this comes from another director, it carries even further weight. It also covers instances where staff are covering sickness, mat/paternity leave and secondments,
- Have two-stage authorisation set up on online banking so that another member of staff is required to authorise all payments before release,
- Have policies and procedures; if the company has a stance that no payment request will be accepted via email or telephone, then when one is, they can politely decline and tell it is a fraudulent request,
- Contact your bank as soon as you are made aware funds have been sent. The banks have a duty of care to work together to stop and recover funds for individuals that are subject to fraud.
Internal fraud
All businesses put trust into their staff to do the right thing by the company; if owners don’t, they restrict their opportunities and often get bogged down in tasks they could delegate.
Most individuals are not calculated fraudsters, but some are opportunistic. It is often easy to hide your fraudulent ways if you are the only person working, or with authority, in your department. Internal fraud, fraud committed by the company’s staff, can be the hardest to spot and the most devastating. It often leaves the feeling of betrayal for the businesses owner and the feeling of guilt for the remaining staff due to not spotting the issue. There are too many ways of committing fraud, but there are some key characteristics to watch out for.
Prevention
- Educating all staff that it is not always the colleagues they would expect to commit fraud that do. They should keep an eye out for:
• Changes in their colleague’s behaviour; seeming quiet or secretive,
• A change in a colleague’s personal circumstances, which may cause them to require cash or feel desperate,
• Changes in their colleague’s buying patterns or them living a lifestyle you would deem to be outside of their means,
• Changes in their colleague’s pastimes, i.e. gambling, drinking or drugs. - Make sure that not only one person has access to sensitive data or access to monies, and that dual authentication as a minimum is implemented,
- Make sure that both security and monitoring are in place. Employing a suitable IT consultancy can be a worthwhile investment,
- Create a culture where staff can ask for support and guidance when they have life events that may require work support; this may be the difference between them reaching out and them stealing from you.
- Also, create an environment where staff can speak up about their colleagues in an anonymous fashion.
Impersonation scams
Where a fraudster impersonates a professional body such as a bank, the police, IT security firm or a utility provider and dupes the employee into transferring cash, entering sensitive information or downloading malicious software.
This type of scam can be devastating for the individual involved. The fraudsters are often very good at what they do, will pick their timing impeccably, often meaning the company only realises once it is too late.
A common approach is the fraudsters call confirming that the companies systems are at risk of attack, and they need to move funds to a safe account. They will often call from a supposed known number and have done their research to know which organisation to call from (bank details and accountant details are usually easily found at companies house) and contact the correct employee to deal with the issue.
Prevention
- Make sure that dual authorisation is set up for all outward payments, meaning another colleague will need to question the reason and sign off the payment,
- Educate staff, often just taking some time to consider their situation, will make them think something doesn’t feel right. Making staff aware impersonation scams are a thing is the first step; the second step is to empower them to challenge if they feel something is not right. Empower your team to request the caller calls a director or hangs up and calls the company back on a number, and to an individual, they know.
Unauthorised fraud types
Malware
Malware, ‘malicious software,’ is the term given to any software designed to harm or exploit. Fraudsters will aim to gain access to your system via many different methods, but the two main ways are:
- Phishing emails/ texts – emails with an embedded link or attachment that contains a virus.
- Using an external drive, like a USB stick. These can be plugged in, and unknowingly to the member of staff, contain a virus. Fraudsters are innovative in their approach and have been known to drop USB sticks next to a director’s car; a supportive colleague picks it up on their way into work, plugs in the device to confirm it is the directors and infects the computer system. But it can be as simple as a member of staff plugging in their personal device that doesn’t have the same security level as your internal system.
Malware comes in many forms (see ransomware below), but it is always embedded in the system to cause harm or exploit. Malware can provide false screens, mirror websites and many other things. The fraudster may not act straight away, and some malware will lay dormant in the computer system for some time. Unwittingly the staff member continues about their standard processes while the fraudster can watch and read everything they do. This is particularly dangerous if the staff member has bank access and sole authorisation to amend payees or send payments.
Fraudsters can gather all the login information required to access online banking, create a new payee with their fraudulent account details and send themselves money. If the individual that has been compromised, only has the ability to amend payee details, then the fraudster may lay and wait for the day before the company’s monthly payment run, amend all the payee details to theirs and when the payments are made the business is unaware until their suppliers make contact requesting payment.
Prevention
- Implement good quality IT security, and restrict the ability to download software to only those who need it,
- Create a culture that asks staff to think twice before they take action and consider risk,
- Educate and test staff; some organisations send test emails with links imbedded to educate staff on how easy it can be to open the business up to attack.
Ransomware
A type of malware particularly devastating for businesses. The ransomware is delivered into a system in any of the ways noted above; it then sets about freezing the system or locking the files/ data held on it. The company/ individual is then contacted requesting a ransom; usually, money, to release the system/ data. Ransomware, being a type of malware can spread through a company’s system and, with the reliance on technology to run most businesses these days, make many inoperable.
The fraudster can often take some time to make contact, so the business starts to feel the true impact. The sums requested as ransom can be significant as well as the loss of income throughout the process.
Prevention
- Back up all files and data to a remote server so that systems can be wiped, cleaned and reloaded,
- Insure against the risks; insurance companies will have negotiators that will deal with the fraudsters on your behalf, hoping to gain a better deal,
- Make sure firewalls and procedures are robust, preventing the malware breach.
Summary
With all these types of frauds education, robust systems and processes and an open culture can reduce the risk. Educate staff to be vigilant and suspect all transactions until confirmed genuine. The police and banks are backing the Take 5 Campaign, suggesting that taking time to think before taking action can help you clarify your situation.
Fraudsters are very good at what they do. Prevention is the best method of protection, but quality insurance can be the difference between a company surviving an attack and continuing to trade after.
Care for individuals
Outside of the business community, it is important to consider the vulnerable when thinking about fraud. As technology and security continue to improve, fraudsters are turning to scams and deception to dupe people into handing over their cash. Educating family and friends is the easiest way to limit the impact.
Frauds to make more vulnerable family members aware of:
Investment Fraud
A fraudster calls pretending to be from an investment company, often with an investment too good to be true. The individual is tricked into sending monies, they think will be invested, to the fraudster. Often only when the investment is due to mature or the welcome pack the individual was expecting doesn’t arrive do they realise what has happened.
Online purchasing fraud
Often through an online auction or from an unknown seller or website, goods are purchased which never arrive. Always ensure purchases are made from reputable sources and paid for in a way which provides protection against such frauds.
Deception fraud
As above, the individual is called by someone pretending to be from a professional organisation, i.e. a bank or the police and suggests their money is at risk and they should move it immediately. The individual then transfers funds to the fraudsters account and is told to leave it there until they make contact again.
Romance/ friendship fraud
Individuals are befriended by fraudsters who build romantic relationships or friendships over an extended period. Once the bond is strong, they request cash support, this can be to live and get by, or it can be as extravagant as they are stuck in a foreign prison and require bail money, or are flying over to see them and need money for flights. These types of frauds are not uncommon and can be devastating for families that see life savings disappear.
This article was produced by Matt Hector, Business Development Manager at Price Bailey. To contact Matt about any of the points raised in this article, please get in touch using the form below.
Could the Kickstart scheme support your recruitment strategy in 2021?
COVID-19 continues to impact the labour market, with continued employer uncertainty, we have seen record numbers of redundancies. With further lockdown restrictions expected, one of the hardest-hit brackets is the 16-24-year-olds.
Some of our hardest-hit sectors, leisure and hospitality, are heavy recruiters of this age bracket; and with thousands leaving full-time education with limited employment prospects the Government have stepped in and hope to generate them opportunities.
How does the Kickstart scheme work?
The Kickstart Scheme is available to employers of all size and provides funding for 25hrs per week, per employee for 6 months. The funding covers the vast majority of the employment costs:
- 100% of the National Minimum Wage (or the National Living Wage depending on the age of the participant)
- associated employer National Insurance contributions
- employer minimum automatic enrolment contributions
The job placement must be new and filled by young people (aged 16-24-years-old), who are currently on universal credit; and at risk of long-term unemployment.
Eligibility criteria for the Kickstart scheme
To qualify for the scheme placements must:
- be new jobs
- must not be in replacement of existing vacancies or self-employed contractors;
- be for a minimum of 25 hours per week for six months
- must pay at least National Minimum Wage
A second applicant may take a placement after the first has completed their six-month period. Funding is only available for candidates introduced through the scheme; direct applications to the employer will not be considered.
When the scheme was first launched employers had to make at least 30 placements available between when the scheme opened, in November 2020, and December 2021. This would have ruled out many smaller employers, so on the 25 January 2021 the Government removed this requirement.
Wishing to create the biggest impact with the scheme, when the 30 minimum rule was in place businesses where allowed to pool their requirements with other companies through Kickstart gateways. These were organisations such as local authorities, charities or trade bodies that could take applications from multiple employers and make one application for over 30.
Even with the need to recruit 30 removed from 3 February 2021, it may still be worthwhile using your local gateway for support due to their experience of applying for the scheme. They are still open and willing to help.
Funding for the Kickstart scheme
| Instalments | Grant sum payable | Payment date/milestone |
| 1st payment | One £1,500 payment per Participant for set-up and support costs* | On confirmation to DWP’s satisfaction that the Participant has started employment with the Grant Recipient. |
| 2nd payment | 100% of the Relevant Wage for 25 hours a week of work by the Participant during the first month of the job, plus the associated employer National Insurance contributions and employer minimum automatic enrolment contributions. | Paid in arrears – on confirmation that Participant paid through pay-as-you-earn tax (PAYE) for the first month. This payment is expected to be in or around the 6th week of the placement. |
| 3rd to 7th payments | 100% of the Relevant Wage for 25 hours a week of work by the Participant during the subsequent second, third, fourth, fifth and sixth months of the job, plus the associated employer National Insurance contributions and employer minimum automatic enrolment contributions. | Paid in arrears – approximately every month after the 2nd payment on confirmation that Participant paid through PAYE for the previous month. |
* 1st Payment up to £1,500 per placement for setup costs, support and training. This includes IT equipment, software licences, uniform, PPE and admin and management time.
There will be ongoing monitoring, making sure that the funds are being spent as expected and that the employee is gaining the relevant skills pitched at the start of the application. This scheme is to provide young people with quality roles in organisations, and they are expected to help learn skills for future employment. Companies should make sure they have the resource to respond to any such data requests. The compliance checks we have seen regarding the CJRS suggest that the checks are extensive and can be time-consuming for employers, so having well-documented systems and procedures in place will support.
Employers must also commit to develop the skills and experience of each applicant, which should include supporting them in areas such as:
- Looking for long-term work;
- CV and interview preparation; and
- Basic skills such as attendance, timekeeping and teamwork.
Applications for the Kickstart scheme
The scheme is live, and applications can be made through the Government website:
Sole application for 30 placements or more: https://www.apply-kickstart-grant-employer.service.gov.uk/
Applications where a Kickstart gateway is required: https://www.gov.uk/guidance/apply-for-a-kickstart-scheme-grant-29-or-less-job-placements
Once your application is successful:
- You will be requested to provide DWP with job descriptions that work coaches at Jobcentre Plus will use to match suitable candidates for the job placements.
- DWP will send you the candidate details.
- You will then be able to interview the candidates matched to your job placements.
- You then select the candidate best suited to the role.
Applications will be considered by a panel who will only agree to provide the funding if the job placements meet the eligibility criteria.
The current aim is to respond to applications within one month of submission, and successful employers will receive a grant agreement detailing how much funding will be provided which they will need to sign and return before the placement can begin.
This article was written by Matthew Hector, Business Development Manager, who can be contacted for any further information.
Funding support
Applying for a loan during the COVID-19 outbreak
COVID-19 has had a similar impact on the UK economy as a recession would. No one can reasonably predict how long this impact will be felt; so how can businesses produce projections that lenders can rely on?
To help answer this, Lee Sharman, Sebastian Humberston, Molly Rushworth and Matt Hector combined their knowledge of management accounts, forecasts, corporate finance, lending and investment to put together this short guidance article.
Most lenders will want to see the three items below. This article explains more about points 2 and 3 and then shares a live case study:
- The last three years’ finalised accounts – the purpose of this is to show that pre-COVID-19 you had a viable business that could have repaid the proposed borrowing. Therefore, should there not be any material impact on the business in the long term, the business can repay in the future.
- Up to date Management Information (MI) – MI bridges the gap between the finalised accounts and projections. MI is important as it will show continued trading up to the point of COVID-19.
- Projections & cash-flow forecast – lenders will appreciate that this may be difficult to predict currently, but they will want to see that you have thought about it and documented your expectations. 6 months is the term most lenders are suggesting will be the impact period for businesses.
Management Information (MI)
Demonstrating to a funder that you have a solid grasp of your financial performance is crucial when trying to secure funding. You don’t need to be an accountant, but you do need to be able to show that you get timely, powerful, financial information that helps you make informed decisions. The circumstances that COVID-19 has given rise to only heighten the importance of this. One way management teams will need to demonstrate their understanding is through the provision of quality MI. Below we have highlighted some of the key differentiators that we believe make up ‘quality’ MI.
- A clear and robust breakdown of performance on an income and cash basis will enable the intended audience to assess the historical and therefore likely future viability of the business. Tracking monthly, and in some cases weekly, changes, in a clear format, can be essential to inform you, and a lender, of your performance. This enables funders to assess the business’ decision-making capabilities and managements’ operating, financing and investing priorities. The reader is not only interested in the overall picture of performance, but that the underlying reasons behind performance trends are the product of strategic decisions and not a fluke. You might be able to use this information to highlight:
– Which customer groups remain strong and which are struggling;
– What activity, if any, is driving revenue growth;
– What gross margin changes have occurred;
– The rationale behind making, or not making, cost reductions;
– Where your cash pinch points are and commenting on what will improve/worsen the situation;
– The impact of government schemes such as the Job Retention Scheme and VAT deferral;
– Demonstrating that you can service debt costs with profits.
- Your nearly ‘real-time’ balance sheet Stock, debtors, creditors and cash are all key. MI that can quickly tell a story regarding each of these components to short term trading is very powerful. For example, a business that sells products might create MI that shows stock both by monetary value and quantity by SKU and then relate this back to product sales, margins or customer payment speeds in order to demonstrate to a lender how the business can ‘create’ cash. Similarly, MI that highlights the age of creditors and perhaps has comments on the ability to agree delayed payment will help demonstrate a company’s ability to retain cash. Every company in need of further funding will have a different balance sheet story to tell if you do need advice, then please reach out to us.
- Key Performance Indicators (KPIs) are an important source of narrative reporting as they explain the business’ progress towards its stated goals. They also show the quality of the director’s judgement in really understanding what drives the business. In normal circumstances, KPIs are often a mix of financial, commercial and people-based data. Today, there may be additional ‘short term’ KPIs which are also needed. There may also be industry-specific KPIs that a business would be expected to report against. A bank will want to see that this has been carefully considered, especially if appraising and business in a sector that carries perceived risks in a recession, for example, construction.
- Link to budgets and projections. Too often, reporting is still perceived as a post-event, reflective exercise and is simply filed away once completed. However, with the increased mainstream use of cloud accounting software, mind-sets are shifting to realise that performance, and reporting is a live event that can be tracked. Therefore, when building projections, the starting point should be working from current performance and not a named point in time where a business can achieve the things it wants to achieve. One simple way to ensure that you can easily link your MI to projections, other than through software packages as mentioned above, is through a well-considered nominal code structure that is sustainable, not only for the day-to-day management of the business but that a set of forecast assumptions can be built from. This ability to show budget vs actual performance is important in demonstrating that the company has, and can, deliver on its plans.
- Quick and agile reporting processes. The speed at which businesses are able to extract MI, at a standard that can be understood easily, will reflect on the perception of managements’ own grasp of performance. Cloud accounting software provides options to businesses for both reporting and projections. Remember though that reporting (whether utilising software or not) is only as good as the information input. If the right information hasn’t been captured at the point of entry, is incomplete or includes errors, then the reporting and any projections are going to be unreliable and therefore less effective.
Projections
Projections will need to consist of a profit and loss, balance sheet and cash flow forecast. Making sure to keep these in the same format as your year-end accounts and MI, to allow for trend and year-on-year comparisons by the bank.
- We suggest projecting performance for a minimum of 12 months. For a Coronavirus Business Interruption Loan Scheme (CBILS) application, the bank will want to understand expected revenue and the direct costs. In addition, by understanding your non-discretionary fixed cost, minus any Government grants/schemes, they can assess your funding requirement. Most lenders appear to be looking to cover these costs for six months, although they will look beyond this to understand the cash required to get the business back to a cash generative position. At this point, they will then calculate service ability, so projecting over a longer trajectory would be best.
- Projections are only as strong as the supporting assumptions. The bank will understand that you cannot predict how long the impact of COVID-19 will continue for, but if your assumptions are in-depth and well thought out, it will show that you have considered the variables and have a sound understanding of your business and industry. Our suggestion is that supporting narrative to the numerical assumptions is key, as this both provides vital context and demonstrates the management teams understanding of how to guide the business through these times.
- Linking projections and MI. The bank will compare your projections to your management information in the first instance to understand what changes there are. Consider if you have made any cost reductions, any large clients that will not survive the pandemic, and the speed at which revenue will pick up as you trade out of the pandemic. If there are differences between your MI and projections make sure these are detailed in the assumptions; show calculations if required.
- Be realistic. Don’t be tempted to provide a rose-tinted view of reality. The banks will understand that there are ‘ups and downs’ in a business life cycle and will have their eyes open to the fact that there may be a reduction in revenue or an increase in costs over this time. Don’t leave the downs out; the bank would rather know what is coming and the business’ plans to counteract the issue, rather than buy into an unrealistic forecast.
- Ensure your projections derive from inputs, not outputs. When looking at a borrowing requirement, business owners will often have an idea of the size of the facility required. The tendency is then, to base your projections on this amount. Our advice is to focus on the inputs. This will then drive a true profit figure and therefore, true funding requirement. This can often be far larger than the figure you expect.
The key thing to remember is that, if you had a viable business prior to COVID-19, the banks are there to support.
You can learn more about preparing appropriate financial projections in our Financial Modelling podcasts.
Remember this should be a last resort
Government schemes should be the last lending resort for a bank. What this means is that business owners will be asked to look at all alternative measures to reduce their working capital issue. This will include:
- Utilising all the Government initiatives available such as grants, rates relief, Tax and VAT deferrals and the employee job retention scheme.
- Banks will expect business owners to take practical steps such as removing any discretionary costs from the business, reducing directors salaries and dividends and having discussions with creditors (and landlords) regarding owed funds.
In return, the banks will look at quick, short term funding solutions. These may include capital payment holidays on current facilities, increased / new standard overdrafts and, if available, standard bank lending. These options often release cash far quicker than a loan with Government backing, with overdrafts and capital payment holidays often taking effect next day.
We are awaiting updates on the stance underwriters will take, and it is also too early for us to understand the timescales involved between application and drawdown. Some banks state that once a loan offer has been accepted, they expect a 45 day SLA until the Government security is confirmed and drawdown of the loan can take place.
Covenants and financial due diligence have not been noted by the banks. Both these measures are implemented by the lenders at certain debt levels or circumstances. A CBILS loan, for instance, is still a loan and if the banks have standard levels they would introduce measures such as these, we would imagine that they will continue to do so. We will add more information on this as we learn of it.
Live case example
There are still a lot of unknowns surrounding the placing of the government-backed CBILS money. However, we have provided an overview of the current projection process we are going through with an existing client as this may provide some insight into how best to prepare your application.
What can you say with certainty?
- Revenue – If your business has been forced to close its doors until further notice, then its ability to generate income will be significantly diminished if it hasn’t completely disappeared. In this circumstance revenue, and therefore cash receipts, should be relatively simple to predict at least in the short term. Similarly related direct costs should be predictable with a degree of accuracy, so long as you have a good handle on your fixed vs variable costs.
- Creditors – In the short term you may be able to agree payment holidays with your existing lenders, landlords and certain trade creditors, however, the extent to which each of these are willing, or able, to support you is more difficult to predict – so have these conversations as early as possible. Projections should reflect the agreements you have been able to agree with certainty, with prudency built-in beyond this temporarily agreed period of relief.
- Tax liabilities – HMRC are being particularly supportive with companies encountering cash flow difficulties as a consequence of COVID-19, typically agreeing to a minimum of 1-month payment freeze. However, we have heard this freeze is likely to be extended to 3 months where required, with the accumulated liability as at the end of the freeze period being spread across 6 to 12 months.
What is less certain, and what is reasonable to assume?
The speed with which your business may be able to build back up to a ‘business as usual’ level of trading is something which is much more difficult to predict. In the specific case, we refer to above, the directors have prudently assumed a staggered approach over a four-month period to build back up to previously budgeted figures. This staggered period comes after a three month zero-revenue period to June 2020.
Predicting the willingness and ability for suppliers, landlords and lenders to continue forgoing or delaying payments are highly subjective. When building projections and deriving the funding requirement, we suggest adopting prudent approximations of the support you will receive. Erring on the side of caution will hopefully mean that a successful loan application first time round will be sufficient to see you through this period of uncertainty — a far better position to be in than having to submit a second application for additional funds.
Key questions to consider and information to prepare before approaching your lender
Each scenario will be different, but here are some questions businesses should be prepared to answer:
- How much would you like to borrow? How did you get to this figure?
- How long would you like the loan for? 1-6 years. The term will likely impact the interest rate charged.
- Provide a detailed breakdown of how the funds will be utilised. Taking care that not too high a percentage is being used for director’s salaries/dividends.
- What action have you taken to date to reduce costs? Detail any Government / local authority grants or schemes. Include non-discretionary spend that has already been cut and can be cut.
- What were your fixed monthly costs before the pandemic, and what are they now following any support/action to reduce costs as above?
- Do you foresee any long term impact on the business? Detail how the business will “trade out” of the situation. Be honest; the bank will want to know the full extent.
- What is your “Plan B” should the loan not be approved?
- Have you considered other borrowing options such as overdraft increase/selling assets / using commercial credit cards as an alternative?
- How much capital has been introduced by the shareholders and/or directors?
- What is the impact on your supply chain? Have you reviewed their contingency plan?
- What is your debtor concentration? Taking your top 5 clients, what percentage of your turnover are they? And how have they been impacted by COVID-19?
Price Bailey’s specialists are on hand to support, existing client or not. If you would like any further information or support on anything discussed above, please contact us on the form below.
Ongoing Government support in a post-pandemic world – the Recovery Loan Scheme
One thing that you cannot deny throughout the COVID-19 pandemic is the Government’s sustained efforts to try and support businesses and scaffold the economy in a time of significant uncertainty. As the country moves toward a normality that resembles life pre-pandemic, many businesses are asking what support is available for those still feeling the impact and for those who are wishing to maximise on opportunities available to them.
In March, the Government announced the closure of the Bounce Back and Coronavirus Business Interruption Loan schemes; and introduced the Recovery Loan Scheme to provide continued financial support to businesses across the UK as they trade out of the pandemic.
The scheme is open to any business that has been affected by COVID-19, and the use of funding is unlimited, provided it is for a legitimate business purpose. Businesses can borrow up to £10m per business (or up to £30m for groups). Businesses will also be happy to hear that you can still access this scheme, even if you have accessed other Government support schemes such as the Bounce Back scheme, CBILS or CLBILS. However, the amount available to borrow under the RLS will be reduced by any borrowing from previous schemes.
The scheme provides guarantees to lenders via several different facility types:
- Term loan
- Overdraft
- Invoice finance
- Asset finance
It is important to note that not all lenders are accredited to offer all types of facility.
Businesses seeking to apply for the scheme should ensure they have sufficient debt capacity to take on any additional funding of this kind. In addition, we strongly advise that you (with support from your advisors, if required) take the time to appropriately plan and produce a robust cash flow forecast to ensure that:
- there is a legitimate requirement for the funding
- you know to what level funding support is required
- that the business is in a position to service the debt
This is relevant for any business considering the scheme, but particularly to those businesses that have already accessed other Government support schemes (or other commercial debt facilities) and are yet to understand the true amount of their repayment commitment fully; and/or whose turnover/working capital continues to be impacted by the pandemic and is variable upon the success of the easing of social distancing restrictions. This is also particularly relevant as, as with other external finance applications, you will need to be able to provide a solid business case for the funding, proving you will be able to meet the repayment obligations.
So how does RLS work?
The RLS will be available through named lenders accredited by the British Business Bank. Further accredited lenders may be added as the scheme continues, and you can view the current list on the BBB’s website. However, lenders are advising that you speak with your existing finance provider first before approaching these lenders, as they may be able to offer you a commercial loan on better terms.
Key features of the scheme:
- The scheme will remain open until at least 31 December 2021, subject to review.
- There is also no maximum cap set for the amount available to lend to businesses through the scheme – so there is no need to rush to apply if you do not feel you require financial support in the immediate term.
- There is no minimum or maximum turnover restriction for businesses seeking to access the scheme.
- The upper limit of the facility provided to each business is £10m (and up to £30m across a group), with minimum facilities starting at £1,000 for asset and invoice finance, and £25,001 for term loans and overdrafts. (Please note – individual lenders will set their own minimum and maximum limits within these ranges).
- The scheme gives the lender a government-backed guarantee against the outstanding balance of the facility.
- The annual rate of interest, upfront fee and other fees cannot exceed 14.99%, and businesses are required to meet all costs, interest payments and fees associated with the facility.
Term lengths:
- Term loans and asset finance = 3 months – 6 years
- Overdrafts and invoice finance = 3 months – 3 years
- If you borrow £250,000 or less, personal guarantees will not be taken by the lender. For borrowings over £250,000, personal guarantees are at the lender’s discretion. Still, the maximum that can be covered is 20% of the outstanding balance of the RLS facilities after the proceeds of business assets have been applied.
- Lenders can offer an RLS facility to those businesses that would either not gain the funding on standard terms or would do but at a higher rate without the benefit of the government-backed guarantee.
- In contrast to other Government support schemes, the RLS will not include 12-month Business Interruption Payments (BIP) to cover interest payments.
Our advice to those looking to access the scheme:
While this next stage of Government support for businesses is being welcomed, business owners should remember that it is still a loan that needs to be repaid. Its purpose is to support with working capital requirements or to support growth. Lenders will be looking for you to be confident in and provide suitable evidence to support that the funding will be used to help the business grow, further benefiting the economy with jobs and supply chain benefits.
It is also worth remembering that there is no cap on the funding available to all businesses. The scheme remains open to applications until 31 December 2021; therefore, there is no immediate need or panic to apply for funding. Instead, it is better to take this time to develop your business’ recovery plan properly, revisit your strategy, and put together a robust set of financials to identify what, if any, funding requirements you have. This may start with improving working capital efficiencies, cutting further none essential spending and equity or other debt funding options (aside from RLS). This will mean that not only will you potentially avoid taking on further debt unnecessarily, but also, if applying for RLS is the right thing for your business’ recovery, you will be adequately prepared for lenders’ due diligence.
Coronavirus Business Interruption Loan Scheme (CBILS)
The Coronavirus Business Interruption Loan Scheme (CBILS) offers loans of up to £5m. It will provide lenders with a Government-backed guarantee for 80% of the facility issued, therefore making many more lending applications viable in the eyes of the lenders.
There is no requirement for applicants to have had a normal commercial loan application rejected. It is currently expected that any applicants who have applied and received funds on normal commercial terms in response to COVID-19, will have these facilities retrospectively “rebooked” as CBILS loans. Applicants should, of course, confirm this with the lenders at the earliest opportunity.
Personal Guarantees (PGs) will not be required by the lender for loans below £250k, and some of the 80+ accredited lenders on the scheme are waiving this requirement altogether.
For loans above £250k, PGs may still be required, at the lenders’ discretion, however, they will be capped at 20% of the outstanding loan value (to account for the government guarantee). Further, CBILS does not allow a lender to take a security over the Principal Primary Residence of the business owner.
The borrower is always liable for all of the debt and must demonstrate that, were it not for the current pandemic, they would be viable and creditworthy.
The Government will also make a Business Interruption Payment to cover the first 12 months of interest payments and any lender-levied fees so that businesses will benefit from no upfront costs and no payments for 12 months due to capital payment holidays.
Many of our clients and contacts are using a combination of government solutions. The speed at which funds are received from all the initiatives depends on the provider. Client feedback is that once the lender is satisfied and the offer issued, then funds are received relatively quickly. CBILS is further ahead than others, but it still may be advisable to consider other immediate sources of cash such as overdraft extensions and payment holidays to manage short term challenges until funding comes through. If charges are required on property/debtor book/leases, and legal support is required then this will delay proceedings.
We are unsure of the date that the scheme will end and applications must be made, but it was initially thought it would be six months from opening meaning 27 October 2020.
The lenders remain extremely busy; businesses with a serious urgent need will need to be prioritised. The Price Bailey team are in regular contact with many of the banks. Just like their clients, bank staff have learned in real-time with significant operational constraints and have been under a lot of pressure to deliver.
From our discussion with the mainstream lenders, we understand that their priority is to support the UK economy, and businesses, to trade through these difficult times. That being said, they must remain responsible lenders and will therefore only be looking to lend money to the businesses that they are confident can repay the debt in line with its agreed terms, once trading has returned to normal.
The majority of lenders are suggesting that applicants speak with their relationship manager in the first instance. Some lenders are asking businesses to complete an application form prior to approaching their relationship manager. This will likely detail previous years trading, the impact of COVID-19 and how the business plans to return itself to normal trading.
It is likely an average of the last three years of financial accounts and up to date management information, to the point of the virus, will be required.
Our advice is to undertake a detailed assessment of short term liquidity and speak to a relationship manager in the first instance.
Eligibility criteria
To be eligible for support via CBILS, the business must:
- Be UK based, with a turnover of no more than £45 million per annum
- Generate 50% of turnover from trading activity
- Have a borrowing proposal which, were it not for the current pandemic, would be considered viable by the lender, and for which the lender believes the provision of finance will enable the business to trade out of any short- to-medium-term difficulty
- Operate within an eligible industrial sector
- Have not received “de minimis State Aid” beyond €200,000 equivalent over the current and previous two fiscal years.
There is not currently a consistent approach from Lenders regarding the eligibility of businesses which meet the above criteria but which have overseas or Private Equity ownership (whole or part). We expect that a broad approach will be adopted, but applicants should be aware Lenders are reviewing each business on an individual basis, and it is at their discretion how they will appraise each scenario.
Several lenders have also stated that they will not offer CBILS loans to new customers.
Key Facility Features
The table below summarises the key features of available products under CBILS.
| Product
|
Max value
|
Max term
|
Other features
|
| Overdraft & revolving facilities | £5m | 3 years | Loans limited to 25% of 2019 Turnover or 2 x annual wage bill, whichever is greater
Interest-free period of 12 months paid for by the Government, some leaders are also providing capital payment holidays of up to 12 months No guarantee or arrangement fees for SMEs Incorporate limits – 10k – £5k Sole trader and partnerships – £25,001 – £5m |
| Invoice finance facilities | |||
| Asset finance facility | 6 years | ||
| Term loans |
Security
All banks on the CBILS scheme offer unsecured lending for facilities of £250,000 and under.
For facilities above £250,000, the lender can decide what it needs for security; however, this cannot be the PPR of the borrower. Consequently, approvals for facilities under £250,000 are expected to be quicker.
How to apply?
CBILS applications must be made directly to a British Business Bank (“BBB”) accredited lender. In the first instance, they should approach their own provider via their relationship manager or relationship director as this will prove the quickest way to access funds.
The majority of the mainstream banks will only supply CBILS facilities to their current clients. Businesses ability to “shop around” may be limited, however, we do know lenders that will look at new business.
Almost all sectors are eligible – except for; Banks, Building Societies Insurers, The public sector including state-funded primary and secondary schools; Employer, professional, religious or political membership organisation or trade unions. There may be caps for specific other industries.
A business will only be eligible where they can confirm that they have not received “de minimis State Aid” beyond €200,000 equivalent over the current and previous two fiscal years. Most State Aid is notifiable and will be carved out from this, for example, EIS and R&D tax credits.
However, some grants and other government assistance received by typically innovative businesses which are not notifiable state aid can be classed as de minimis (this is often specified in grant documentation), and an example of this is funding under the Horizon 2020 scheme.
How do I evidence I have a viable business?
The team at Price Bailey have good relationships with banks as well as a list of questions that are useful to answer before approaching a lender. Please do not hesitate to contact the Price Bailey team if you have any questions or believe we may be able to assist you.
You must show in your borrowing proposal that were it not for the COVID-19 pandemic, your business would be considered viable by the lender, and for which the lender believes the provision of finance will enable your business to trade out of any short-to-medium term difficulty.
According to UK Finance, the benchmark for assessing viability or profitability for within a CBILS Application is 31 December 2019.
There will be many viable businesses that may be unable to show this (for example, through recent investment for growth, higher R&D expenditure or a turnaround and restructuring plan). Such applications will need to clearly set out the underlying reasons within their applications to enable the individual underwriter to take a fully informed view.
The process of proving serviceability is built from understanding the fundamentals from the previous year’s financial accounts, and bridging the gap between these and the projections/budgets.
Pre-profit or loss-making businesses are less likely to be successful in a CBILS application and may be better suited to raise equity finance, rather than debt.
Price Bailey is experienced in raising funds for many different situations, demonstrating viability is something we often get asked to support in.
To find out more, please contact Simon Blake, who leads our Strategic Corporate Finance team.
Trading subsidiaries, the pandemic and their financial support
One of the common dilemmas facing charity trustees as a result of the pandemic is how to manage their trading subsidiaries. As these subsidiaries are usually set up for tax-efficient profit generation, they may hold very little in reserves as all profits are gifted/covenanted to the charity each year within nine months of their year-end.
Profitable trading subsidiaries have usually managed their working capital and cash flow through this nine-month window after their year-end to allow them to create more profits and working capital before fully distributing their prior-year profits to their parent charity. Overall, most subsidiaries have been able to operate in this way without the need for additional loans or investment from their parent charities.
However, during the pandemic and COVID-19 restrictions, many were unable to generate profits – not able to open shops, hold events, run conferences or otherwise trade. Therefore these profitable ventures were losing money – retail grants and furlough may have helped, but some unavoidable fixed costs meant that these entities were making losses. Some are continuing to be loss-making as they still cannot trade. So what do they do? There are no reserves to fall back on as they were all given away.
Trading subsidiaries that have overall net funds can be technically insolvent. Negative funds do not necessarily mean creditors cannot be paid when they fall due as the trading subsidiary may have longer-term debt or loans, which mean it can pay its creditors.
Investment in subsidiaries through loans, working capital and share capital
The Charity Commission updated its guidance on advice to charity Trustees in their coronavirus COVID-19 guidance for the charity sector in April 2021 and specifically picked on this issue regarding trading subsidiaries. https://www.gov.uk/guidance/coronavirus-covid-19-guidance-for-the-charity-sector#trading-subsidiaries–financial-support-from-parent-charities. This clarifies that the parent charity must consider any support and funding provided to its trading subsidiary the same as any other investment on an arm’s length basis. Hence the Trustees must consider the financial return on their investment, which means assessing the financial viability of the business – its profitability, forecasts and business plans – as part of that investment decision whether the funding is provided through a loan agreement from the parent charity, investment in share capital or temporary working capital provided by an inter-company balance which operates on normal payment terms. The share capital route requires stringent review as investing in a struggling trading subsidiary in this way risks the share capital. In contrast, a loan may be able to be secured on assets and can also earn interest. In the worst-case scenario, should the trading subsidiary need to formally close, a secured loan would have a better chance of a payout, whereas a capital injection would not be last to be repaid, if at all.
In normal times, and when first setting up a new trading business, such business plans and income generation projections/profitability are used by the charity to justify the ability to invest in that trading business and then reap the future rewards. At the start of the pandemic, and when lockdowns were lifted, the business plans were updated which expected a return to a viable, profitable business in a relatively short timescale and often within a year. Hence investment from charities to support these viable trading businesses meant charities did inject ‘capital’ into their trading subsidiaries on the basis that these funds would be returned in the near future and generate appropriate returns.
The landscape has now changed again; confidence in the economy fully opening up and allowing large scale conferences and events remains uncertain. The future of some business activities and their return to profitability is less predictable, and businesses which require international visitors and predicting their return is difficult. Even shops and hospitality that are currently open are not certain to continue as variants cause concern over the further easing of government-imposed restrictions. Will the vaccination programme prove successful against variants and allow businesses to return to a level of normality? Trustees looking at investment in trading subsidiaries face difficult decisions; furlough continuing until September may offer some assistance in their decision making by perhaps deferring discussions on the future viability of businesses until a later point. Continued investment and support of their trading subsidiaries may, on balance, still be justifiable by charity Boards for the moment. However, it may be appropriate for Boards to engage professional advice to help support their decision making at this critical time. The charity Trustees must put the interests of their charity first when looking to provide financial support and its justification as an investment. Charities cannot support and invest in failing businesses; hence it is essential that any support provided to their trading subsidiary has a clear business case and supporting documentation to evidence due diligence by the charity Board in making their decision to fund. It is equally important that the charity Board monitors the situation to ensure that the basis of any decision remains sound and that if the situation changes, appropriate action is taken immediately.
Going concern
With charities currently going through their audit process, such as with March 2021 year ends, the going concern perspective on the charity and its trading subsidiary may require attention.
As already noted, the trading subsidiary may have overall deficit funds (net liabilities). It is technically insolvent, albeit that it may have cash to pay its creditors as they fall due through the use of the working capital/loan provided by the parent charity. The charity cannot guarantee the debts of a trading subsidiary that is not delivering primary purpose charitable activity as this would be using charitable funds for non-charitable purposes.
It is commonplace instead for the charity to provide a support letter. Typically, such support letters confirm that the charity will not require repayment of any of its balances owed by the trading subsidiary for at least 12 months from the date of signing the accounts unless funds allow. Whether such a support letter is sufficient to support a going concern perspective for the trading subsidiary will require forecasts, cashflows and budgets to show that the trading subsidiary will return to profitability or the resources it has, are sufficient to survive for at least that 12-month window. If there is doubt over its future viability, then this may cause a detailed discussion with the auditors and management to consider and understand the implications on the accounts and/or audit report.
Therefore, in considering the ability for the trading subsidiary accounts to be prepared on a going concern basis, there will need to be evidence on how it will be funded and will survive – be it through further cash injections from the parent charity, a return to profitability or being mothballed until better trading conditions are available, or a combination thereof. Negative funds (or formally equity) does not necessarily mean insolvency as the company may be able to still meet its debts as they fall due but does need careful management. Depending on their circumstances, advice from insolvency practitioners may be required where that situation changes.
Conclusions
Trading subsidiaries continue to cause concerns due to the pandemic in terms of their financial support, viability and going concern status. Many now have negative funds at their latest balance sheet date, which brings a heightened responsibility on the directors over future potential insolvency and going concern issues, and future forecasts and projections may be difficult. Ensure you communicate your challenges with your professional advisers and keep them informed and take advice as the need arises. Trustees must ensure that any financial support provided to the trading subsidiary is based on sound business plans, which are closely monitored to ensure that the charity’s funds are not put at risk.
This blog was written by Helena Wilkinson, a Partner at Price Bailey. If you have any questions regarding this blog, you can contact Helena using the form below.
The Future Fund: 10 terms and what to do next
On 20 April the Government announced the launch of a £250m Future Fund to provide matched funding using a Convertible Loan Note (CLN) to high growth companies that may be pre-revenue or pre-profit.
A business is considered eligible for the fund if:
- it is UK-incorporated – if your business is part of a corporate group, only the parent company is eligible
- it has raised at least £250,000 in equity investment from third-party investors in the last five years (from 1 April 2015 to 19 April 2020 inclusive)
- none of its shares are traded on a regulated market, multilateral trading facility or another listing venue
- it was incorporated in the UK on or before 31 December 2019
- at least one of the following is true:
- half or more employees are UK-based
- half or more revenues are from UK sales
The British Business Bank (BBB) is an administrator of the scheme, which opened for applications on 20 May 2020.
The key terms:
- The convertible loan is at most equal to the funding provided by private third parties at exactly the same terms – this means that the funding from the third parties cannot be issued as equity.
- The size of the government cheque will be at least £125,000 and at most £5m.
- This is bridge funding for working capital purposes only – no dividends, bonus’, adviser fees, consultant fees etc. The Government was very clear about the purpose of this loan being a bridging loan with commercial terms. Thus, the founders should keep this in mind when considering this option as it is not intended to be seen as state aid rather another funding option available.
- Like for like terms, it is very important to note that the third party investment needs to match the terms and conditions of the government loan. Therefore, it is not eligible for EIS relief. This was a big shock to the start-up community and Angel Investors since it narrowed the pool of the companies that could benefit from the Future Fund even more.
- The CLN turns into the most senior class of shares when:
- In the future, the business raises further capital that is equal to the whole bridge funding round;
- On sale or IPO;
- After 36 months, the loan will likely turn into shares, or, be repaid with a premium. From the conversation with the government agencies, it was indicated that the government expectations are to convert the loan into shares rather than be repaid. It seems that the Government is taking a VC approach to this loan and hopes for some winners.
- Conversion will be at a 20% discount to the conversion event’s share price. In English, this means, when the loan converts to equity, the Government get a 20% share price discount (i.e. more shares). This is similar to most CLNs or Advance Subscription Agreements (ASA).
- The interest rate on the loan is 8% pa unless investors lend at a higher rate. The interest does not compound and does not convert into equity.
- The company will have to provide limited warranties including in respect of title and ownership, capacity, its loan eligibility in accordance with the government eligibility criteria, the borrowing facilities of the company, compliance with the law, litigation and insolvency events to the lenders on closing of the loan.
- Covenants look quite light though there is a Most Favoured Nation clause which means that if someone else invests and gets better terms than the Government, then their terms must be improved to match.
- The ability to raise further debt that is more senior (and in reality, this CLN is very junior, so most new debt will be more senior) is restricted to new external stakeholders only.
What does this mean:
- Turning to existing shareholders – the Future Fund is a Government initiative that is clearly not there as a solution for all the early-stage companies affected by Covid-19. If you don’t meet the criteria or you are not willing to accept the commercial terms set by the Future Fund, then it might be a good time to reach out to your current investors with a rights issue offer. They are collective owners of the business; thus, it is in their interest to help business to weather this period. Our advice is to ignore preference shares and quirky instruments of the past to avoid mismanaging the point on the most senior class of share and instead focus on the ‘real’ ordinary shares in the business.
- Alternatives for new investors – to reach out to the new set of investors might be an appropriate next step for the majority of the companies but in these circumstances, a new arrangement and deal structures might be used by investors to hedge their risks. For examples, a private investor wants a discounted share price, and EIS relief too. In this case, you could run an Advance Subscription Agreement that provides cash now in exchange for shares issued later at the same 20% discount to a future event’s share price (but without any interest paid along the way). ASAs don’t always comply with EIS rules, though. They can be argued to be a loan and, with newer ‘Risk to Capital’ tests, the 20% share price discount may be viewed less favourably. There will still probably be a way to get EIS compliant ASAs agreed for many businesses, but it will take longer, cost more in adviser fees and all sides – including the investor – will have to be happy with the risks.
- New fundraising activity – new fundraising activity is happening and considering the limited number of companies that are eligible for the Future Fund majority of the companies will be increasingly looking at this option. This suggests that it can continue and, indeed, continue with some success. However, the investors are taking longer to evaluate the companies and are much pickier when making their investment decisions. Therefore, it is more important than ever to show how the business is adapting to the circumstances accompanied by a proper financial model, a fully diluted ownership table in different scenarios and have valuation research. This will allow and support investors in conducting thorough diligence.
- £250m won’t go far – the Future Fund is far smaller than other Government initiatives, and already 58% (as of 14/6) of its funds have been allocated since the applications opened, and applications are only open until the end of September 2020. Worth keeping an eye on various initiatives that are being considered, such as expanding Regional Angels Programme (administered by BBB) in order to address the funding gap that remains for the majority of the early-stage companies.
If you need advice on structuring the ASA, a rights issue or assistance with equity fundraising, then please contact us on the form below.
Why the lesser-known Trade Credit Reinsurance Scheme could be one of the most important Government support packages to date
The scheme is arguably one of the most effective and important support schemes introduced by the Government, yet perhaps oddly, has been one of the least publicised over the last three months. This may be because it is less tangible than the cost savings and cash injections businesses have been receiving; however, without it, the economic fallout could be far-reaching and extreme.
The Government launched the Trade Credit Reinsurance Scheme in June 2020, which
- Underwrites up to £10bn of Trade Credit Insurance (TCI) policies;
- Operates from 1 April 2020 to 31 December 2020 (with the potential for extension)
It is open to all TCI insurers currently operating within the UK market.
The scheme acts as a state-backed reinsurance policy for insurers and (subject to certain conditions) enables them to provide TCI where the private credit market is unable to do so.
It enables insurers to carry on providing trade credit insurance despite the COVID-19 pandemic.
Ongoing delays
Whilst the TCI scheme was announced in May 2020 it is yet to be implemented. It is understood the European Commission has objected to certain elements of the scheme on State Aid grounds, consequently, the scheme is not yet in operation.
We can see a real-world example of the severity of this issue. As a direct consequence of this, Coface, one of the largest credit insurers has withdrawn credit terms for a number of food and drink wholesalers, effectively meaning some wholesalers are now having to pay upfront for goods.
One case is reported to have lost a credit limit of £500k overnight, a significant cash gap.
It is easy to see how such loss of credit terms could create a “perfect storm” and a cash flow crisis as government support is withdrawn, as many wholesalers will already be managing significant wastage losses and bad debts as a result of lockdown.
Wholesale will not be the only industry affected, as noted above, TCI underpins the smooth operation of the UK supply chain. Ongoing delays will result in businesses facing a double-whammy of:
- Manage the cash impact of reduced or no credit terms; and
- Reduced availability of funding solutions to bridge any gap.
It is still hoped the state aid issues can be resolved quickly and the scheme will be introduced as planned, which will allow credit terms to return to more usual levels. However, the longer the delay, the more urgent the issue becomes.
The sooner the TCI scheme can be put in place the better.
What is trade credit insurance, and why is it so important?
TCI is an essential part of the UK supply chain and lending markets.
TCI is a quiet but critical foundation of the UK economy. The Government estimates that £350bn of UK economic activity is underwritten by TCI schemes with 630,000 businesses using TCI each year.
TCI is an insurance product which protects businesses against the risk of non-payment from customers. If the customer does not pay, the insured receives a pay-out under the policy. Larger insurance providers predominantly underwrite it.
By insuring themselves at a relatively low premium, many businesses and invoice finance lenders have confidence they will be paid, even if their customer is unable to do so.
TCI plays a vital role in the UK supply chain (both domestic and export) and in sectors such as recruitment and manufacturing, where payment terms will regularly be 90 days +. Many SMEs also rely on invoice finance as a source of working capital to bridge the gap between supply and payment.
The impact of COVID-19
COVID-19 and resulting uncertainty have had an immediate, negative impact on the revenues and cash flows on many UK businesses, increasing their credit risk profiles. As a result, TCI insurers were less able to offer terms on companies that are too high a risk, or premiums would have increased to such a level as to make them cost-prohibitive.
There are two main impacts:
- SMEs may not supply customers where they were not assured of payment or where the premium was too expensive;
- The lending market (particularly invoice finance) would be severely restricted as lenders would not advance funding without the protection of TCI.
If not addressed, there would have been a severe impact on liquidity and working capital rippling down the UK supply chain, caused by slower payments and lower levels of funding.
The impact would potentially cause a seizure of the UK supply chain, and a significant wave of business failures as cash reserves rapidly dwindled.
How can the scheme help?
- The scheme will maintain liquidity and working capital levels with the UK supply chain for thousands of UK businesses, by enabling them to access insurance pay-outs in the event of customer default, non-payment or insolvency;
- The scheme has “unlocked” the invoice finance market which had been temporarily constrained by the increased risk of lending without trade credit insurance. It has increased of invoice finance providers that are able to lend to SMEs (including taking on new customers and under the CBILS scheme).
Many SMEs will be forecasting or experiencing cash flow pressure due to COVID-19 through slower or lower revenues and the withdrawal of other government support schemes. These SMEs now have access to a broader range of funding options (including CBILS) as a result of the scheme.
For businesses that currently have (or are forecasting) a funding requirement/increase in working capital requirements possibly due to;
- Expansion or growth opportunities, during or post-pandemic;
- A restart and return to “normal” operations;
- Funding a longer-term turnaround and/or restructuring of existing funding facilities;
Invoice financing may well be an agile, cost-effective option, and one well worth considering. Thanks to the Trade Credit Insurance Scheme, it is back on the table.
This article was written by Matt Howard, at Price Bailey. If you have any questions regarding the Trade Credit Insurance Scheme or invoice finance funding, please contact Tim on the for form below.
Legislation
Evicting a tenant and the implications of the Coronavirus Act 2020
UPDATED: 3 September 2020
The Coronavirus Act 2020 came into force on 26 March 2020 as an emergency measure in response to the spread of the coronavirus. Notice periods in relation to possession proceedings for certain residential tenancies were extended with the aim of protecting residential tenants from eviction for the relevant period.
On 29 August 2020, the Coronavirus Act (Residential Tenancies: Protection from Eviction) (Amendment) (England) Regulations 2020 came into force. These apply to England only. They extend the relevant period and dis-apply certain parts of the original Coronavirus Act 2020.
We have answered some of the most common questions we have received below regarding evictions in England.
Q: Can I still serve a s21 notice on my tenant to terminate the tenancy at the end of the fixed term?
A: Yes you can but the notice period to be given in a s21 notice has increased once again from 29 August 2020, from three to six months. An amended prescribed form 6A has also been produced.
Q: What if my tenant is in rent arrears or committing another breach of tenancy?
A: The notice period to be given before possession proceedings can be commenced with a section 8 notice has also been extended in most cases to six months. Shorter notice periods will apply to certain cases where the landlord wants to evict the tenant because of rent arrears of six months or more, anti-social behaviour, domestic abuse or fraud.
Notice must be given on a new ‘Form 3’ which has been amended to reflect these changes.
Q: How long will the requirement to provide these extended notice periods last?
A: The current legislation dictates that the extended notice periods are to be used until 31 March 2021. However, provision has been made to extend these notice periods further, either as a whole, for different purposes or in different areas as required (perhaps to reflect a phased release from ‘lockdown’).
Q: What if a notice was served before 26 March 2020 or before the changes introduced on 29 August 2020?
A: The provisions are not retrospective. Accordingly, notices served with shorter notice periods before the changes were implemented are still valid.
Q: Can I start or continue with court possession proceedings during the ‘lockdown’?
A: A new Practice Direction was brought into force on 27 March 2020. Possession proceedings are currently suspended until 20 September 2020. This suspension period has already been extended once and may be extended further if necessary. In theory, landlords can start court proceedings for possession orders after a notice has expired. However, our experience indicates the Courts will not even serve the proceedings until the suspension is lifted.
Q: Does the tenant’s obligation to pay rent continue after a tenancy or notice has expired?
A: Yes. Whilst the tenant remains in occupation, they remain liable for rent in accordance with the tenancy agreement.
Q: Are rent arrear (debt) claims affected?
A: While non-possession court claims have not been formally suspended, delays are being experienced by court users and particular applications are being given priority over others. Claims for rent arrears can be commenced but landlords must be prepared for delay; these claims are not considered high priority.
Q: As a landlord, am I still liable to carry out repairs during the lockdown?
A: Landlords remain legally obligated to ensure properties meet the required standards so urgent, essential health and safety repairs should be made. Local authorities have been encouraged to take a pragmatic, risk-based approach to any complaints from tenants and consider the current difficulties landlords may encounter before taking enforcement action
This post was written by Heidi Berry, a Lawyer at Price Bailey. If you require any further assistance or have any other questions, please contact Heidi on the form below.
Temporary suspension of company strike-off and dissolution
Companies House announced on 16 April 2020 that it will temporarily ‘pause’ the strike-off process to prevent companies being dissolved. These measures are in addition to the those already announced, allowing a business to apply for a three-month extension to their accounts filing deadline.
A company may apply to Companies House to be struck off the register and dissolved if it is no longer needed and meets specific eligibility criteria. For companies currently making an application for Voluntary Strike-Off, the proposal will still be registered at Companies House and a notice published in the Gazette in the usual way. However, after this point, any further action will be automatically suspended for the time being, meaning that the company will remain an ‘active’ entity.
A Compulsory Strike-Off procedure also results in a company being removed from the Register of Companies but is when a third party commences the application. This is most often instigated by Companies House itself when a business has failed to file accounts or annual statements.
The announcement is an essential response to the current pandemic because, from the date of dissolution, any assets of a dissolved company will be ‘bona vacantia’. This means that the assets no longer have a legal owner, so technically become the property of the Crown. The company’s bank account will be frozen and any funds held will also be passed to the Crown via the Treasury Solicitor. With the current difficulties being experienced by many business owners, it is easy to see a situation whereby a large number of companies could be dissolved in error leading to a cessation of trading and loss of control of all assets. The measures are therefore designed to give sufficient time to all businesses affected by the outbreak to file documents at Companies House.
When a company is struck off in error, it is possible for a stakeholder to apply for a court order to restore a company. Under certain conditions, a former director or member of the company may apply directly to the Registrar, under a process called ‘administrative restoration’, preventing the need for court involvement. Either way, while a strike-off is capable of being reversed; it can be a time consuming and costly exercise. The recent announcement, therefore, welcomed as a pragmatic response to the current situation.
Additionally, as part of the announcement, Companies House has stated that companies issued with late filing penalties due to reasons relating to COVID-19 will have their appeals treated sympathetically. The government is also set to introduce legislation to ensure those companies required by law to hold physical Annual General Meetings (AGMs) will be able to do so in a safe way, such as by holding them online or allowed to postpone them.
It is worth noting that the temporary changes to the strike-off procedure do not apply to businesses which will be automatically dissolved after a formal insolvency procedure such as Administration or Liquidation.
It is not yet known how long this ‘pause’ on company strike offs will be in place, and it is understood the policy will be kept under review as the broader situation changes.
This post was written by Stuart Morton, a Licensed Insolvency Practitioner at Price Bailey. If you have any questions, please contact your usual Price Bailey point of contact or Stuart using the form below.
What to expect when HMRC compliance check your use of the furlough scheme
Update 09/02/2021
HMRC has just confirmed there was an error on the CJRS calculator on the GOV.UK website which has now been fixed. This error only affects a specific number of claims that contained employees who were not on a fixed salary. If an employer used an employee’s pay for January 2019 as reference pay, instead of January 2020 and the employee’s pay was different in January 2019 to January 2020, then the claims would have been miscalculated by HMRC.
If you think you may have been affected by this, you will need to recalculate and resubmit your CJRS claim by the deadline on Monday 15 February.
Price Bailey calculates its CJRS claims for the vast majority of our clients using our own calculator; so there is no need for clients to resubmit a claim unless they supplied their own claim information to us having used the HMRC calculator on the GOV.UK website and having employees in their claim that meet the criteria above.
If you still have concerns regarding your January claim, please feel free to speak to your Price Bailey contact.
The Coronavirus Job Retention Scheme (CJRS) was first announced back in March 2020 and funds 80% of an employee’s wages if there is no work for them to complete due to COVID-19. For further information and eligibility criteria of the CJRS.
As at 18 October 2020 9.6m employees had been furloughed by 1.2m employers, with a total cost to the UK of £41.4bn; with this number set to rise as lockdown V2 plays out and we hit the winter months.
For those of you that have received State Aid or any other Government or EU grant, you will be aware of the regulation involved in using these schemes. Often a lengthy application process and depending on the size of the grant/ loan possibly ongoing monitoring or a post works review.
Due to how quickly the impact of the pandemic took hold the Government were not able to add red tape to those using CJRS, businesses needed support, and they needed it quick. Therefore HMRC issued the funds but confirmed they might carry out checks in the future. These checks are starting to be completed and are known as ‘compliance checks’. HMRC are requesting vast amounts of information, often, dating right back to the businesses first CJRS claim to confirm compliance.
The checks are there to make sure businesses have met the conditions of receiving the grants, and have claimed the correct amounts. We are aware that HMRC issued ‘nudge letters’ to users of the scheme throughout CJRS V1, to prompt businesses to make sure they were using the scheme compliantly. Not all companies received these letters; and as to whether they were sent specifically to those they suspected to be using the scheme in the wrong manner, possibly due to the size of their claim versus their standard wage bill, or their use of the scheme compared to those in the same sector, or they were sent randomly, we are unsure.
What is involved in an HMRC compliance check?
Our early experience shows these compliance checks come with extensive information requests with very tight timescales; two weeks from the date of the letter to provide the information requested. It is common for HMRC letters to be received with a delay of up to two weeks. Our experience so far is the delays are leaving clients with just days to respond. We have found that HMRC has been supportive once contacted to extend the date but only in the first instance and only for a short time. This means that businesses should be pre-empting these requests and using sound systems to store data and records ready for supply.
The letters note that if on review, whilst compiling the paperwork requested, you spot you have made a mistake then you should contact your compliance officer, noted personally at the top of your letter, immediately. You are also required to confirm a direct contact and the best number to contact this person.
Requests are substantial and are on a per-employee basis. Meaning the more employees that utilised the scheme (9.6m in total across the UK), the more information you are required to provide. Much of the information requested is also per wage payment; meaning those that pay weekly are needing to supply much more information than those that pay monthly.
Information/ evidence that has been requested from the claims we have seen so far (this is per employee and per claim):
- The employees, name, address and NI number
- The furlough start and end date
- Details of how their normal pay is calculated
- How their furlough pay was calculated
- Whether you paid the employee at least the amount on the claim (evidence required)
- The amount paid in pension costs (evidence required)
- The number of hours usually worked
- The number of hours worked
- The number of hours on furlough
- The employer NI contribution claimed
- The employer pension contribution claimed
As well as supplying all the above information, details of any corrections or adjustments to your CJRS claims are also required. All the information is to be supplied electronically by email to your named contact and confirmation that you understand the risks of sending sensitive information electronically is required separately and before sending.
We are yet to see compliance checks of the legal condition of the grants, i.e. contract amendments and furlough agreements but understand these were a clear and well-documented stipulation of receiving the grant.
We are yet to see any trends in the sector or size of business and expect for consistency HMRC will include a variety of business in different sectors, of different sizes and with varying levels of claims. What we do know is that when a compliance check is carried out, considerable time is required to gather the information requested, both from a business’s internal team and their professional support.
How can you mitigate the cost of an investigation?
Price Bailey proudly offer a Tax Investigation Service, an annual insurance policy that reimburses our professional costs should our clients have an HMRC tax investigation regarding:
- Self-assessment full or aspect enquiry
- Personal affairs of directors/ partners
- Employer compliance disputes
- IR35 disputes
- VAT Disputes
- Schedule 36 enquires
The Price Bailey Tax Investigations Service provides for reimbursement of up to £125,000 of professional fees in the event of an accepted claim on our practice policy. Importantly this covers investigations into CJRS.
This article was written by Matthew Hector, Business Development Manager at Price Bailey. For any further information on HMRC compliance checks with regards to the Coronavirus Job Retention Scheme, you can contact Matt using the form below.
Self-Employment Income Support Scheme (SEISS) grants
26 March 2021
The Government has recognised the ongoing impact that COVID-19 has had on self-employed individuals and have announced that there would be a fourth grant, which will be available in April 2021.
At the Budget in March, the Chancellor confirmed that he would set the fourth grant at 80% of the average trading profits across three months, paid out in a single instalment, capped at £7,500.
SEISS fourth grant
The fourth grant will also take into account 2019/20 tax returns and will now also be open to those who became self-employed in the tax year 2019/20. Doing this gives many other individuals access to much-needed funding.
Eligibility for the scheme will now be based on your filed 2019/20 tax return, which may also affect the amount of the fourth grant, which could be higher or lower than previous grants you received. Your trading profits must be no more than £50,000 and at least equal to your non-trading income, and you must also have submitted your 2019/20 tax return by 2 March 2021.
You must either:
- be currently trading but are impacted by reduced demand due to coronavirus
- have been trading but are temporarily unable to do so due to coronavirus
You must also declare that:
- you intend to continue to trade
- you reasonably believe there will be a significant reduction in your trading profits due to coronavirus
HMRC’s online claim service for the fourth grant will be available from late April 2021 until 31 May 2021. If you are eligible, HMRC will contact you in mid-April to give you a date from which you can make your claim.
SEISS fifth grant
The Government also announced that there would be a fifth and final grant covering May to September, which you will be able to claim from late July (if you are eligible).
The amount of the fifth grant will be determined by how much your turnover has been reduced from April 2020 to April 2021.
The fifth grant will be worth:
- 80% of 3 months’ average trading profits, capped at £7,500, for those with a turnover reduction of 30% or more
- 30% of 3 months’ average trading profits, capped at £2,850, for those with a turnover reduction of less than 30%
HMRC will provide further details on this fifth grant in due course.
Over the past 12 months, many smaller businesses have experienced trading difficulties but have ambitions of returning to a sense of normality.
Such grants could well be what you or your business needs in current circumstances, whether to provide living costs, working capital, paying other debts, or investing in new equipment.
Support for newly self-employed
Many thousands of individuals have also commenced Self Employment in the tax year 2019/20 and unfortunately could not claim the previous SEISS grants. The new criteria mean that those can now claim a much-needed cash grant.
This article was written by James Elvin, Manager at Price Bailey. For any questions regarding this article, you can contact James on the form below.
Price Bailey response
Interview: Martin Clapson discusses whether staff need to return to the office right now on BBC Radio Cambridgeshire
From this week, employers can insist that staff return to the workplace as long as enough safety measures are in place to guard against the spread of the coronavirus and they make businesses COVID-secure. It marks a shift from previous government advice telling people to work from home if possible.
Price Bailey has approximately 370 members of staff currently working from home. Martin Clapson spoke to Chris Mann on BBC Radio Cambridgeshire yesterday from his home in Newmarket to discuss whether staff really need to return to the office right now.
Chris Mann
Martin Clapson is the Managing Director of Price Bailey, a leading chartered accountancy firm based in Cambridge. Martin, now you’re talking to me from home in Newmarket. Are you planning to stay there, or are you all going back to the office?
Martin Clapson
No, I’m planning to stay in Newmarket, and we have no serious plans to send our teams back to the offices.
Chris Mann
If we’d had this conversation back in February, and I said we’d be talking in August, and you’d be telling your staff that they can all work from home, would you have imagined that Martin?
Martin Clapson
No, I wouldn’t have imagined I’d be telling them that they should continue working from home. We have had, for a number of years actually, something called Smart Working where we’ve said to our teams that we don’t mind you working from home or remotely from the office as long as you get the work done. I don’t believe I would have said, back in February, that I would want everyone to be working for home, so that is a big change.
Chris Mann
Have you had to give them any extra equipment or do anything different for them?
Martin Clapson
Most of the teams already had IT equipment at home because of Smart Working, but not everybody did. We had to work quite hard in March to ensure that everybody had laptops and dual screens. We told them that they could take their office chairs home and even said to a few people that if they wanted to take their desks apart and take them home, then they can. We want them to be as comfortable as possible.
I’m not complaining about the productivity of our teams working from home.
Martin Clapson
Chris Mann
In terms of productivity; before, during and now in the period after lockdown, with people being encouraged to go back to work, how has productivity gone in those phases?
Martin Clapson
It’s over four months since the end of March when we went into lockdown, and I think productivity at the beginning was good. At the end of April, the start of May time, I think people started to feel a little bit down thinking this is the long term. I was quite naive to think we could be back by June. Thinking I’m going to be doing this for say eight weeks, ten weeks, and I think once we got to about May you realise this is more for the longer term, so I think people felt a little bit down and productivity did decline a little bit.
We’ve worked really hard to keep the motivation going with lots of communications. To be honest, I think I’ve seen certain Price Bailey people more in lockdown than I did before, with using Zoom and Microsoft Teams so I think we’ve worked quite hard on the communications. I think now people have got used to it and productivity is good. I’m not complaining about the productivity of our teams working from home.

Chris Mann
Of course, there is the whole issue of contact not just with each other, but with your clients, so what do you do about that?
Martin Clapson
Right from day one, we’ve encouraged our team members to spend as much time contacting our clients, whether they want that to be done by telephone or by Zoom calls and to just keep that contact going as much as possible.
I think the worst thing for clients and for our teams is to feel lonely and I think we are there to help our teams and our clients as much as possible. I think you can do that by just keeping the communication going as much as possible.
Chris Mann
Now you’ve got headquarters in Cambridge, but there are many big companies based in London. I think Barclays have got 6,000 people. Do you think people will go back at all, in those kinds of numbers, to big offices like that again?
Martin Clapson
Many of the big banks are saying to their team members, don’t expect to be back working from the offices until at the earliest Christmas or even March next year; obviously, the branches are open, but at the head offices they are very cautious, and that’s one of the reasons why Price Bailey is very cautious in getting our teams back.
The number one priority for any managing director and for any boss is the health and safety of their teams, and I do worry about having our teams working from offices where you can’t open the windows, and it is air-conditioned. It’s tough. It’s fine for the Government and for other business leaders to say get teams back working but is it safe, is it really safe? How do we know whether somebody’s got COVID-19 or just a cold unless you can get the test done really quickly? I think our teams are working fine from home.
I think big companies are seeing that their teams are working fine from home, so why is there the big rush to get them working out of offices?
As a human race, we’re very good at adapting to circumstances.
Martin Clapson
Chris Mann
I had to talk to my GP last week so didn’t go in and didn’t have an appointment, we did it on the phone, and we could have done a Zoom call. Just a few months ago you would have thought that’s not satisfactory, but actually, it does work Martin doesn’t it?
Martin Clapson
As a human race, we’re very good at adapting to circumstances. Don’t get me wrong. I don’t believe that we’ll be working from home and we’ll be seeing GPs from a distance forever, but I think it could be a balance in the future. Sometimes you need to be in the office to work, and sometimes you can work from home. Sometimes you’ll need to see the GP face to face, and sometimes you can do it by telephone. That flexibility is going to be really good for society going forward.
Chris Mann
You’re the boss of a big international organisation [IAPA] as well as part of Price Bailey but, dare I say it, lunches are a big part of your business, entertaining, going to things, sponsoring and so on.
Martin Clapson
My view is, how can you look after and give great advice to a client unless you spend time with them? Get to know them. Get to know their family. Get to know what their problems are. Then you can give them the financial solutions which suit them and their family.
You can only do that if you spend time with people, and I think you’ll struggle to get that kind of deep knowledge and awareness of a client by doing it virtually. We are missing that side of it, and we do need to get back as quickly as we can, but we can see clients outside and socially distance. I just don’t think we need our teams working from officers at the moment to do that.
 This interview was recorded as part of Chris Mann’s show, Afternoons on BBC Radio Cambridgeshire on 3 August 2020. You can listen to Afternoons on BBC Radio Cambridgeshire with Chris Mann airs Monday to Thursday from 2 pm on 95.7FM, 96 FM and on digital radio.
This interview was recorded as part of Chris Mann’s show, Afternoons on BBC Radio Cambridgeshire on 3 August 2020. You can listen to Afternoons on BBC Radio Cambridgeshire with Chris Mann airs Monday to Thursday from 2 pm on 95.7FM, 96 FM and on digital radio.
Price Bailey’s response to COVID-19
There is no doubt that many of you are concerned about how this pandemic will affect your business day-to-day and the impact on any upcoming strategic decisions. Please remember that we are here to support you with any immediate planning or personnel questions you might have, however small. Your Price Bailey contact will be happy to talk through your concerns and work with you to find the right solution for your business, so do give us a call.
As a result of the Government’s decision to move the country into a national emergency lockdown to mitigate the impacts of the virus, and the associated advice and restrictions on social contact, we have decided to close all Price Bailey locations from the morning of 24 March 2020.
Our Board, partners and teams were well prepared for this scenario.
You can be assured that we have a robust business continuity plan in place, which will enable us to minimise the impact on our service to you. Since the beginning of the outbreak, we have been making preparations for our people to work from home, and mobile telephone numbers have been added to the website for most contacts. No matter who you speak to, or what day of the week it is, you can be confident you’ll always get the same experience.
Please take care of yourself and those you hold dear.
Rolling updates – Last updated: 04 March 2021
Coronavirus Job Retention Scheme (CJRS)
Update 09/02/2021
HMRC has just confirmed there was an error on the CJRS calculator on the GOV.UK website which has now been fixed. This error only affects a specific number of claims that contained employees who were not on a fixed salary. If an employer used an employee’s pay for January 2019 as reference pay, instead of January 2020 and the employee’s pay was different in January 2019 to January 2020, then the claims would have been miscalculated by HMRC.
If you think you may have been affected by this, you will need to recalculate and resubmit your CJRS claim by the deadline on Monday 15 February.
Price Bailey calculates its CJRS claims for the vast majority of our clients using our own calculator; so there is no need for clients to resubmit a claim unless they supplied their own claim information to us having used the HMRC calculator on the GOV.UK website and having employees in their claim that meet the criteria above.
If you still have concerns regarding your January claim, please feel free to speak to your Price Bailey contact.
Offered from the 01 March 2020, the CJRS has been a lifesaver for many businesses during the pandemic. It has taken various forms throughout its time. For further information on how the scheme was initially launched as well as the terms and eligibility.
The scheme has been tailored to support businesses depending on the trading environment at the time. During the summer of 2020 the scheme started to be phased out with its terms less favourable to employers, making them more inclined to return staff to work if possible.
As the pandemic took further hold and the UK saw further lockdowns, the scheme was revised which made it more favourable again to employers and employees, allowing more jobs to be saved.
The full 80% of employee wage scheme was made available again from the 01 November 2020.
Then in the budget March 2021, a further extension to the scheme was announced of 6 months from the 31 March. The first 3 months of the extension maintains the terms we have known throughout the winter with 80% of an employee’s wages fully funded by the grant.
From 01 July the Governments grant percentage will reduce monthly, and the employer’s contribution will increase to maintain the 80% of pay to the employee.
|
|
May
|
June
|
July
|
August
|
September
|
|
Government contribution: wages for hours not worked
|
80% up to £2,500 |
80% up to £2,500 |
70% up to £2,187.50 |
60% up to £1,875 |
60% up to £1,875 |
|
Employer contribution: employer National Insurance contributions and pension contributions
|
Yes |
Yes |
Yes |
Yes |
Yes |
|
Employer contribution wages for hours not worked
|
No |
No |
10% up to £312.50 |
20% up to £625 |
20% up to £625 |
|
For hours not worked employee receives
|
80% up to £2,500 per month |
80% up to £2,500 per month |
80% up to £2,500 per month |
80% up to £2,500 per month |
80% up to £2,500 per month |
Employees and employers do not have to have used the scheme previously to claim but after the 01 July employees must continue to receive 80% of their pay to be eligible.
Claims need to be submitted by the middle of the following month for the previous months furloughed hours.
For periods ending on or before 30 April 2021, you can claim for employees who were employed on 30 October 2020, as long as you have made a PAYE RTI submission to HMRC between the 20 March 2020 and 30 October 2020, notifying a payment of earnings for that employee.
For periods starting on or after 1 May 2021, you can claim for employees who were employed on 2 March 2021, as long as you have made a PAYE Real Time Information (RTI) submission to HMRC between 20 March 2020 and 2 March 2021, notifying a payment of earnings for that employee.
We are aware that HMRC are completing ‘compliance checks’ on a selection of businesses that have used the scheme to make sure that it has been used in line with its conditions and the correct amount has been claimed.
Job Support Scheme (JSS)
On the 24 September 2020, in a further attempt to reduce the impact of COVID-19 on the economy, businesses and jobs, the Chancellor announced details of the Job Support Scheme (JSS). It should be noted that the official guidelines for the JSS have been withdrawn by HMRC, pending revision.
The scheme was initially due to take over from the CJRS at the end of October, but due to the rising number of COVID-19 cases across the UK, the Government announced lockdown V2 and CJRS V2 to support alongside it, which has effectively postponed the rollout until after 30 April 2021, with no new date being announced yet.
The Coronavirus Job Retention Scheme (CJRS), was due to come to an end on the 31 October with the JSS taking over supporting those businesses still operating with reduced demand. It was designed to drive the 10% of the working population still on furlough in mid-September 2020 back to work in some capacity, and protect jobs that might otherwise be at risk from falling demand.
The scheme is aimed at small and medium-sized businesses with larger businesses subject to a financial assessment test to demonstrate they require government funding. The expectation is that large employers will not be making capital distributions to their shareholders whilst accessing the scheme.
To be eligible, the employee needed to be working at least 33% of their usual hours. This requirement is to formalise the fact that this scheme is to support viable jobs. The 33% was due to be reviewed after the initial three months and was presumably going to be increased. The Government scheme shares some of the cost of the 66% balance of hours not worked. The scheme will pay for a third of hours not worked, with the employer covering another third and the employee taking a reduction in wage to cover the other third.
You can use our JSS calculator to understand the cost to you as a business and the impact on your gross pay as an employee in advance here on our Job Support Scheme calculator.
Kickstart scheme
COVID-19 continues to impact the labour market with unemployment increasing by more than 700k in the first 12 months of the pandemic. Between March 2020 and May 2021 70% of job losses were among under 25s. With continued employer uncertainty, we have seen record numbers of redundancies, with . With long Lockdown restrictions expected, one of the hardest-hit brackets beingis the 16-24-year-olds. Some of the severely affected our hardest-hit sectors, leisure and hospitality, are heavy recruiters of this age bracket; and with thousands leaving full-time education, with limited employment prospects, the Government have stepped in and hope to generate them opportunities.
By the end of January 2021, the Kickstart scheme had created over 120,000 jobs – harnessing the talents of a new generation of young workers.
The Kickstart scheme is available to employers of all size and provides funding for 25hrs per week, per employee for 6 months. The funding covers the vast majority of the employment costs:
- 100% of the National Minimum Wage (or the National Living Wage depending on the age of the participant)
- associated employer National Insurance contributions
- employer minimum automatic enrolment contributions
The job placement must be new and filled by young people (aged 16-24-years-old), who are currently on universal credit; and at risk of long-term unemployment.
To qualify for the scheme placements must:
- Be new jobs,
- Must not be in replacement of existing vacancies or self-employed contractors,
- Be for a minimum of 25 hours per week for six months,
- Must be paid at least National Minimum Wage.
When the scheme was first launched employers had to make at least 30 placements available between when the scheme opened, in November 2020, and December 2021. This would have ruled out many smaller employers, so on the 25 January 2021 the Government removed this requirement.
Wishing to create the biggest impact with the scheme when the 30 minimum rule was in place businesses were allowed to pool their requirements with other companies through Kickstart gateways. These were organisations such as local authorities, charities or trade bodies that could take applications from multiple employers and make one application for over 30.
Even with the need to recruit 30 removed from 3 February 2021, it may still be worthwhile using your local gateway for support due to their experience of applying for the scheme.
For further information, you can read our article: Could the Kickstart Scheme support your 2021 strategy and help you recruit talent?
Local Restrictions Support Grant (LRSG)
Businesses closed due to national lockdown
The Local Restrictions Support Grant LRSG supports businesses that have been required to close due to the national restrictions.
Administered by your local authority, you may be eligible if your business:
- is based in England
- occupies a property on which it pays business rates (and is the ratepayer)
- has been required to close because of the national restrictions
- has been unable to provide its usual in-person customer service from its premises
This could include non-essential retail, leisure, personal care, sports facilities and hospitality businesses. It could also include businesses that operate primarily as an in-person venue, but which have been forced to close those services and provide a takeaway-only service instead.
LRSG counts towards your total de minimis state aid limit of €200K over a 3 year period. If you have reached this threshold, you may still be eligible under the COVID-19 temporary framework.
Grant size will be based on rateable value:
- Property with a rateable value of £15,000 or less, you may be eligible for a cash grant of £1,334 for each 28-day qualifying restrictions period.
- Property with a rateable value over £15,000 and less than £51,000, you may be eligible for a cash grant of £2,000 for each 28-day qualifying restrictions period.
- Property with a rateable value of £51,000 or above, you may be eligible for a cash grant of £3,000 for each 28-day qualifying restrictions period.
You can apply via your local council’s website – Find the website for your local council.
Businesses closed due to local lockdown
A grant up to £3,000 per month is available subject to the business applying having been shut due to restrictions for a minimum period of two weeks (previously three).
Administered by your local authority, you may be eligible if your business:
- is based in England
- occupies a property on which it pays business rates (and is the ratepayer)
- is in an area of local restrictions and has been required to close because of local restrictions that resulted in a first full day of closure on or after 9 September
- has been required to close for at least 14 days because of the restrictions
- has been unable to provide its usual in-person customer service from its premise
For example, this could include non-essential retail and personal services that operate primarily as an in-person venue, but which have been forced to close those services and provide a takeaway-only service instead.
Eligible businesses can get one grant for each non-domestic property within the restriction area.
The precise set of businesses eligible for the scheme may vary between each local council area under local restrictions in recognition of the specific conditions in each area.
LRSG counts towards your total de minimis state aid limit of €200K over a 3 year period. If you have reached this threshold, you may still be eligible under the COVID-19 temporary framework.
Grant size will be based on rateable value:
- Properties with a rateable value of £15,000 or under will receive grants of £667 per two weeks of the closure (£1,334 per month).
- Properties with a rateable value of over £15,000 and less than £51,000 will receive grants of £1,000 per two weeks of the closure (£2,000 per month).
- Properties with a rateable value of £51,000 or over will receive grants of £1500 per two weeks of the closure (£3,000 per month).
The grant will be extended to cover each additional 14-day period of closure. If your business is closed for 28-days, or 2 payment cycles, it will receive £1,334, £2,000 or £3,000, depending on the rateable value of the property.
You can apply via your local council’s website – Find the website for your local council.
Businesses legally open within local lockdown but affected
The Local Restrictions Support Grant (LRSG (Open)) supports businesses that have been severely impacted due to temporary local restrictions.
Businesses that have not had to close but which have been severely impacted due to local restrictions (Local COVID alert levels: High or Very High) may be eligible.
Eligible businesses may be entitled to a cash grant from their local council for each 28 day period under local restrictions.
Local councils have the discretion to provide grant funding for businesses under this scheme. They will use their discretion in identifying the right businesses to receive this funding, based on their application process.
Your business may be eligible if it:
- is based in England
- is in an area subject to ‘High’ or ‘Very High’ local restrictions since 1 August 2020 and has been severely impacted because of the local restrictions
- was established before the introduction of Local COVID alert level: High restrictions
- has not had to close but has been impacted by local restrictions
LRSG counts towards your total de minimis state aid limit of €200K over a 3 year period. If you have reached this threshold, you may still be eligible under the COVID-19 temporary framework.
The grant will be based on the rateable value of your property on the date of the start of the local restrictions. The local councils will be expected to provide funding under the following tiers unless there is a local need to deviate.
- Property with a rateable value of £15,000 or less, you may be eligible for a cash grant of up to £934 for each 28 day period.
- Property with a rateable value over £15,000 and less than £51,000, you may be eligible for a cash grant of up to £1,400 for each 28 day period.
- Property with a rateable value of £51,000 or above, you may be eligible for a cash grant of up to £2,100 for each 28 day period.
Businesses that are not required to close but are impacted may continue to receive funding under LRSG (Open) if restrictions are increased to Local COVID alert level: Very High.
If a national lockdown in announced funding under this scheme will cease.
You can apply via your local council’s website – Find the website for your local council.
Additional Restrictions Grant (ARG)
Vital support for those businesses that have not yet been eligible for funding
Local authorities have been given additional funds to support businesses with Additional Restrictions Grants (ARGs). The scheme is predominantly aimed to support those businesses that have not been eligible for grants previously due to not directly paying business rates; although each local authority is given the freedom to determine their eligibility for the grants.
Previous Local Restrictions Support Grants (LSRGs) have been set amounts based on the rateable value of the premises in which you trade. This means if you did not pay rates, you were not eligible, and a number of business slipped through the Governments support net. ARGs though, are much more flexible with eligibility and the amount of the grant being decided by the local authority, which means it can be tailored to support the local economies.
The Government has released funds on the expectation that businesses that are not legally forced to close but, nonetheless, are severely impacted, benefit from the money; which could include businesses:
- which supply the retail, hospitality, and leisure sectors
- in the events sector
- or those required to close but which do not pay business rates.
With all local authorities having varying criteria, it is difficult to detail how the funds will be administered, but you can find further information about the eligibility in your area here. Local authorities will likely open a window for applications, possibly in multiple phases with different criteria for each so it is important businesses study the local criteria for their area.
The amounts of the loans are expected to be relatively small for the majority but can be up to £10k. Those not eligible are:
-
- those that are trading effectively
- those businesses that are in administration or are insolvent.
VAT
The VAT deferral scheme enabled businesses to defer VAT payments which would have been due for payment between the period 20 March 2020 and 30 June 2020 (i.e. payments in respect of VAT returns due at the end of February, 31 March and 30th April).
The government initially announced that any payments that had been deferred in this period would have to be paid in full by 31 March 2021. However it has since been announced that businesses who did defer payments in that period will be able to opt to pay the debt off in up to 11 instalments over a longer period of time. Instalments can be made up until 31 March 2022 without any late payment interest being charged.
It was necessary to opt into this scheme as it is not automatic and businesses can choose how many instalments to make the payment over. There will be conditions which must be met in order to opt-in, including that you must be up to date with VAT returns and must be able to pay the deferred VAT by Direct Debit.
The application process opened 23 Feb 2021 and are now closed. . If you apply by 19th March you maximise the scheme by paying 11 instalments, by 19th April, 10 instalments and so on until 19th June when the online system closes.
If you do not opt into the scheme and have not agreed alternative arrangements with HMRC, the deferred VAT must be paid in full by 31 March 2021.
For further information or advice please contact Vat Team at Price Bailey.
Support for the self-employed
In the Budget, March 2021, the chancellor announced further phases of self-employed grants. There have been 4 phases of support announced by the Government for the self-employed. Eligibility has been the same throughout the grants. Individuals can apply if 50% of their annual income is derived from self-employed work, and their average annual self-employed trading profit is £50k or less.
The grants are taxable income and also subject to National Insurance contributions.
Individuals will need to prove they have been adversely affected by COVID-19. They do not need to have claimed previous phases to claim the newer phase.
Phase 1 – Grant covering March, April & May, capped at £7,500
The first phase announced 26 March offers individuals a grant of up to 80% of their average monthly trading profits, paid in one lump sum up to £7,500 (£2,500pm).
Phase 2 – Grant covering June, July & August, capped at £6,570
The second phased announced 29 May offered individuals a grant of up to 70% of their average monthly trading profits, paid in one lump sum up to £6,570 (£2,190pm).
To be specifically eligible for phase 3 and 4 individuals must:
- have been previously eligible for the Self-Employment Income Support Scheme first and second phases (although they do not have to have claimed the previous grants)
- declare that they intend to continue to trade and either:
- are currently actively trading but are impacted by reduced demand due to coronavirus
- were previously trading but are temporarily unable to do so due to coronavirus
Phase 3 – Grant covering November, December & January, capped at £7,500, online applications will go live 30 November 2020.
The third phase announced 5 November offers individuals a grant up to 80% of their 3 months average monthly trading profits, paid in one lump sum up to £7,500 (£2,500pm).
Phase 4 – Grant covering February, March & April, capped at £7,500, online applications will go live in late April 2021.
The fourth phase, detail announced in the Budget, offers individuals a grant of up to 80% of their 3 months average monthly trading profits, paid in one lump sum up to £7,500 (£2,500pm).
The fourth grant will take into account 2019 to 2020 tax returns and will be open to those who became self-employed in tax year 2019 to 2020. The rest of the eligibility criteria remains unchanged.
Phase 5 – Grant covering May to September. The amount of the fifth grant will be determined by how much your turnover has been reduced in the year April 2020 to April 2021.
The fifth grant will be worth:
- 80% of 3 months’ average trading profits, capped at £7,500, for those with a turnover reduction of 30% or more
- 30% of 3 months’ average trading profits, capped at £2,850, for those with a turnover reduction of less than 30%
Online applications will go live late July. HMRC will contact you mid-July to give you a date you can make your claim from, if you are eligible from your tax returns. Claims must be made on or before 30 September 2021.
For further information relating to the above grants or any other personal tax issues, please contact Michael Morter.
Funding solutions during COVID-19
The Chancellor, Bank of England, British Business Bank and HMRC created a combination of unprecedented support options for UK businesses throughout the pandemic.
Businesses raised £ 175bn in the initial 6 months of the pandemic environment, and mainstream banks suggest they completed their 5 year planned lending objectives within the first 3 months. Lenders will be keen to make sure that you had a viable business before the pandemic and that you have a strong repayment vehicle. Loans are required to be repaid, and therefore government initiatives such as the CJRS and grants with no repayment should be utilised to their full potential before applying for debt.
There are several options available when it comes to funding your business during COVID-19:
Coronavirus Business Interruption Loan Scheme (CBILS)
Open until the 31 March 2021 in its current form, CBILS offers loans and other lending products of up to £5m, where the Government secures 80% of the facility to provide comfort to lenders.
Loans can be taken over a maximum of 6 years with fees and interest being paid for by the Government for the first 12 months. Most lenders are allowing 12-month capital payment holidays from the start of the loan, so there is no repayment due till month 13. Overdrafts and invoice finance facilities are available for terms of up to 3 years.
Businesses applying for a CBILS loan will need to prove that they had a viable business that could repay the borrowing prior to COVID-19. The monies borrowed will be expected to support the business through COVID-19 difficulties.
For further information and eligibility criteria, read our detailed article Coronavirus Business Interruption Loan Scheme (CBILS) or contact Simon Blake, who leads our Strategic Corporate Finance team.
Recovery Loan Scheme
During the Budget the chancellor announced a new form of lending superseding the CBILS and BBLS. Available from 6 April businesses of any size will be able to apply for:
- Term loans and overdrafts of between £25,001 and £10 million per business.
- Invoice finance and asset finance of between £1,000 and £10 million per business.
Term loans and asset finance can be repaid over up to 6 years, and overdrafts and invoice finance product can be taken over 3 years.
Like CBILS, this scheme offers the lender a Government guarantee of 80% of the facility; making more applications acceptable to lenders. Also like CBILS no personal guarantees will be required for facilities under £250k and a borrower’s main residents cannot be charged as security.
The funds borrowed can be used for any legitimate business use, including investment and growth. Borrowers are eligible as long as they are trading in the UK and can show:
- They are a viable business or would be viable were it not for the pandemic
- They have been impacted by the coronavirus pandemic
- And are not in collective insolvency proceedings
If previous loan schemes have been utilised this scheme is still available. Lenders will have to be accredited to provide the Government-backed facilities and a list of accredited lenders is due prior to the 6 April.
Bounce Back Loan Scheme (BBLS)
Open until the 31 March 2021 the BBLS was designed to administer cash to smaller businesses quickly. Businesses can borrow from £2,000 and up to 25% of their turnover with a maximum loan of £50,000.
If you already have a Bounce Back Loan but borrowed less than you were entitled to, you can top up your existing loan to your maximum amount.
This scheme provides a government guarantee against 100% of the loan. The loans are director lead, meaning the directors of the company confirm their eligibility and request the amount they wished to borrow. The funds have been made available within days of application by many of the lenders. Interest rates are a standard 2.5% after the initial 12 months interest and capital free period.
On the 24 September as part of the Governments Winter Economy Plan, the Chancellor announced that before your loan is due for repayment your lender will approach you to discuss:
- Extending the term of your loan to 10 years (from 6 years),
- Moving to interest-only repayments for a period of 6 months (which can be used up to 3 times),
- Pausing your repayments for a period of 6 months if you have already made at least 6 repayments (you can use this option once).
All of these were offered with the promise that if taken out, your credit score will not be impacted. This will come as a welcome relief to many who face repaying the cash they required in the depths of lockdown.
Companies can transfer loans of up to £50,000 issued under CBILS to the Bounce Back Loan Scheme.
For further information on this initiative, read our articles or contact William Wilson.
Coronavirus Large Business Interruption Loan Scheme (CLBILS)
On Friday 3 April 2020, the chancellor detailed a new scheme, much like CBILS, but for larger businesses that did not meet the requirement of CBILS nor COVID-19 Corporate Financing Facility.
Currently open until 31 March 2021 CLBILS offers funding solutions up to £200m, where the Government secures 80% of the lend. This, as the name suggests, is for larger businesses with an annual turnover above £45m. This scheme can only be accessed if an applicant has been unable to secure regular commercial finance, so it is advisable to contact your lender in the first instance to see what packages are available and suitable.
Lenders will still be expected to conduct their usual credit risk checks. This scheme allows lenders to specifically support businesses that were viable before the COVID-19 outbreak but now face significant cash flow difficulties that would otherwise make their business unviable in the short term. COVID-19 must have impacted firms, and businesses must evidence that the loan will help them trade out of short-medium term difficulty.
The scheme supports a wide range of financing options including short term loans, overdrafts, invoice finance and asset finance. Businesses will remain responsible for repaying any facility they may takeout.
To be eligible, a business must:
- be UK-based in its business activity
- have an annual turnover above £45m
- be unable to secure regular commercial financing
- have a borrowing proposal which the lender:
a. would consider viable, were it not for the COVID-19 pandemic
b. believes will enable you to trade out of any short-term to medium-term difficulty
Businesses from any sector can apply, except for banks and building societies; insurers and reinsurers (but not insurance brokers); public-sector organisations, including state-funded primary and secondary schools.
If borrowing over £50m then business owners must agree to restrictions on dividend payments, senior pay and share buy-backs during the period of the loan.
We are experienced in raising different types of funds for many different situations and demonstrating viability is something we often get asked to support with.
To find out more, please contact Simon Blake, who leads our Strategic Corporate Finance team.
Coronavirus Corporate Financing Facility (CCFF)
Available for at least 12 months from 20 March 2020, and for as long as those businesses who make a material contribution to the UK economy require support in easing cash flow issues.
The CCFF will provide funding to businesses by purchasing commercial paper of up to one-year maturity, issued by firms making a material contribution to the UK economy.
This is the vast majority of the £330bn scheme that was highlighted by the Bank of England and the Chancellor. However, The Bank of England has already warned that many retailers will not qualify due to their credit ratings. As of 1 March 2020, Companies must be able to demonstrate that they were investment grade. Financial companies (which we interpret as institutions rather than services businesses) are not eligible to apply. Commercial Paper issued by leveraged investment or private equity funded vehicles or from companies within groups that are predominantly banks, investment banks or building societies are not eligible if securities are being issued by a finance subsidiary its parent company should guarantee them.
Commercial paper is an unsecured, short-term debt instrument issued by a company.
CCFF will purchase sterling-denominated commercial paper, with the following characteristics:
- Maturity of one week to twelve months
- Where available, a credit rating of A-3 / P-3 / F-3 / R3 from at least one of Standard & Poor’s, Moody’s and Fitch as at 1 March 2020.
- Issued directly into Euroclear and/or Clearstream
Non-standard features such as extendibility or subordination will not be acceptable.
If firms have different ratings from different agencies, and one of those is below investment grade, then the commercial paper will not be eligible. We believe that the minimum facility size is £1m.
Businesses do not need to have previously issued commercial paper to participate. However, it seems likely at this stage that Commercial Paper will need to be listed (i.e. tradeable), and that any dealing counterparties must be appropriately authorised for FSMA 2000. This could create delays, complexity and enhanced compliance requirements for businesses that have not had to manage these type of securities before and therefore be a practical barrier to access.
It was positive to see that the bank will operate in both the primary and secondary markets, subject to the other side being appropriate.
We see this as an opportunity for businesses to not only inject capital to stabilise but also to improve corporate governance and the ability to access wider forms of capital in the mid-term. As concerning as these times are, there is an opportunity here for certain types of businesses.
To find out more, please contact Chand Chudasama from the Strategic Corporate Finance team.
The Future Fund (TFF)
Withdrawn on 31 Jan 2021, TFF took some time to gain momentum, possibly due to understanding and the fact that loans are only classed as approved once the Convertible Loan Agreement document is issued.
TFF provides government loans of between £125k and £5m to high growth innovative companies using a Convertible Loan Note (CLN). The loan will need to be at least matched by funding from private investors, and the company must have raised at least £250k in private third party investment in the past five years.
The CLN turns into the most senior class of shares when:
- In the future, the business raises further capital that is equal to the whole bridge funding round
b. On sale or IPO
c. After 36 months, the loan will likely turn into shares, or, be repaid with a premium.
The business is eligible if:
- it is UK-incorporated – if part of a corporate group, only the parent company is eligible
- none of its shares are traded on a regulated market, multilateral trading facility or another listing venue
- it was incorporated on or before 31 December 2019
- at least one of the following is true:
- half or more employees are UK-based
- half or more revenues are from UK sales
Loans will have an 8% interest rate and looking at the application V approved figures it would seem that criteria are tight.
For information on this initiative read our blog on The Future Fund: 10 terms and what to do next or contact Chand Chudasama from the Strategic Corporate Finance team.
Debt Advisory Service
Many are still trading in difficult environments, and with a cautious approach being taken by lenders, being prepared prior to approaching them could be fortuitous.
Whilst these schemes provided relief to many, in our daily conversations with clients, we observed gaps in the market. Firstly, those with structurally high levels of existing debt. Secondly, pre-profit businesses who may struggle to access CBILS and for whom the normal ‘start-up’ loan support is not sufficient, and where the shareholder base are not able to deploy further equity funding. Thirdly, the sheer levels of debt on-boarded by businesses during 2020 will cause its own issues. Many are going to be expected to repay the debt over relatively short amortisation periods, and still may not be trading at full capacity.
Due to our extensive experience across our strategic corporate finance team, we are well prepared to support business owners through these three difficult circumstances, as well as any other company struggling to raise funding. You can read about the services we have on offer to support you raise, or restructure debt in this difficult climate by reading our Debt advisory services webpage. You can also read how our team supported a client to raise funds in just such an environment in our case study.
Due to the number of headwinds rearing their head in 2021, we expect cash flow to be a concern for many. With us in the deepest recession ever recorded, we hope that the BoE’s predictions of a ‘bounce back’ are correct and the that ill structured debt and rising interest rates do not restrict the UK’s businesses to prosper.
One positive of COVID-19 on the lending market is the innovation that has presented itself; aside from there being many other ways to fund a business other than debt, there are now many lenders providing alternative finance. Please let us know if you feel you may be hindered by debt as you attempt to maximise on future opportunities.
Legal aspect of the Coronavirus Job Retention Scheme (CJRS)
To furlough employees, you need an agreement – The Treasury Direction says that to claim under the furlough scheme, the employer and employee must have agreed in writing that the employee will cease all work (para 6.7). Notification alone is not sufficient. This document also needs to be kept for five years. Further, as stated above, any salary reduction is a breach of contract without express agreement from the employee.
Furlough agreements are required to include the time period for which the employee will be out of work. This time period will likely be the period that the Job Retention Scheme remains in place, subject to a minimum of 3 weeks. If an employee comes back to work after the set period and you do not require them to work still, you can ‘re-furlough’ them for a further period of time.
A furlough agreement is a temporary variation of the contract of employment, and the employees will revert to their normal terms following furlough. However, some employers are using furlough agreements to introduce and agree on permanent changes such as the right to put the employees on short-time working or to lay them off temporarily.
This is a complex area of law, and legal advice should be obtained before making such changes.
In respect of contractual terms which have not been varied by agreement, the underlying contract of employment continues to apply during the furlough period, as do an employer’s statutory obligations which often override contractual terms, particularly around termination of employment, for example, timings of consultation on a collective redundancy process.
Our Employment Law team can draft furlough agreements at a set cost on a per company, rather than per employee basis.
Coronavirus Statutory Sick Pay Scheme (CSSP)
For small and medium-sized businesses with less than 250 employees, two weeks Statutory Sick Pay (SSP) can be reclaimed per eligible employee absent due to COVID-19 (this includes both Coronavirus sickness and isolation absence) on or after 13 March 2020. Employees will not need to present a GP fit note but can be supplied an isolation note from NHS111 online to satisfy their employer.
The Coronavirus SSP Rebate Scheme is now open for employers to make a claim. The process broadly follows the same format as the Coronavirus Job Retention Scheme (CJRS) claims, for those also claiming through CJRS.
The information employers will need to make a claim is:
- Claim period
- Number of employees
- Amount claimed.
In contrast with the CJRS, you are not required to provide the individual employee’s names or NI numbers.
Claims can only be made for periods that have already passed.
Cash collection during COVID-19
With nearly half of all businesses seeing reduced turnover compared to the previous year due to COVID-19, there will undoubtedly be cash flow pressures for some.
In a normal trading environment, 96% of SMEs will have experienced a bad debt, and 70% will have at least one commercial dispute every three years.
The normal process of recovering owed funds can be lengthy, costly and without guarantee of success; because of this, an average of £40bn is written off by SMEs every year. Cash is always important, but now more than ever, business owners need to be recovering and retaining the cash that is rightly theirs.
Escalate dispute resolution and debt recovery, launched in 2017 after 7 years of planning and investment, is a game-changer in its field. It offers a fixed fee recovery with no fees until the funds are recovered and no fees if the case is not won.
Due to its set up, everyone is incentivised to recover funds quickly, whereas, with the normal process open-ended fee structures and hourly rates, that is not always the case. Recoveries of £1k and above are completed, and the case is assessed and agreed to be taken on often with 24hrs. This assessment is carried out for free, so SME owners know if they have a viable case from very early on in the discussion.
Further information, including case studies, can be found on our Escalate webpage.
If the worst is to happen and funds are not recovered due to insolvency steps taken by your client then maximising on bad debt relief is a key consideration. For further information, read our article VAT and bad debt reliefs.
We can help
Contact us today to find out more about how we can help you
